SS7 routing-protocol breach of US cellular carrier exposed customer data
The US Department of Homeland Security recently warned that malicious hackers may have targeted US phone users by exploiting a four-decades-old networking protocol used by cell phone providers around the world, according to a spokesman for US Senator Ron Wyden (D-Ore.). Meanwhile, the spokesman said, one of the nation's major cellular carriers recently experienced a breach of that same protocol that exposed customer data.
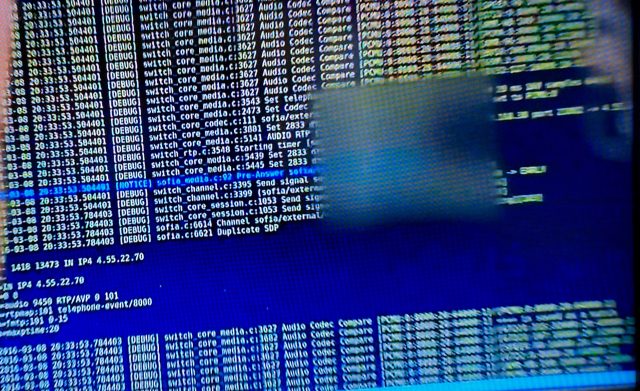
Short for Signalling System No. 7, SS7 is the routing protocol that allows cell phone users to connect seamlessly from network to network as they travel throughout the world. With little built-in security and no way for carriers to verify one another, SS7 has always posed a potential hole that people with access could exploit to track the real-time location of individual users. In recent years, the threat has expanded almost exponentially, in part because the number of companies with access to SS7 has grown from a handful to thousands. Another key reason: hackers can now abuse the routing protocol not just to geolocate people but, in many cases, to intercept text messages and voice calls.
SS7 already being exploitedIn a letter Sen. Wyden received last week, DHS officials warned that "nefarious actors may have exploited" SS7 to "target the communications of American citizens," Wyden spokesman Keith Chu told Ars, confirming an article published Wednesday by The Washington Post. On Tuesday, Wyden sent a letter to Federal Communications Commission Chairman Ajit Pai that heightened concerns of SS7 hacks on US infrastructure.
Read 9 remaining paragraphs | Comments