Hewlett-Packard has alerted some customers that it will be revoking a digital certificate used to sign a huge swath of software-including hardware drivers and other software essential to running on older HP computers. The certificate is being revoked
because the company learned it had been used to digitally sign malware that had infected a developer's PC.Wahlin said that it appears the malware, which had infected an HP employee's computer, accidentally got digitally signed as part of a separate software package-and then sent a signed copy of itself back to its point of origin. Though the malware has since been distributed over the Internet while bearing HP's certificate, Wahlin noted that the Trojan was never shipped to HP customers as part of the software package.
"When people hear this, many will automatically assume we had some sort of compromise within our code signing infrastructure, and that is not the case," Wahlin told Krebs. "We can show that we've never had a breach on our [certificate authority] and that our code-signing infrastructure is 100 percent intact."
Windows SysAdmins: before you laugh yourself to sleep over all those Linux systems struggling to patch Shellshock vulnerabilities, a recently discovered flaw in Windows Powershell
allows similar privilege escalation with very little work. The recently discovered vulnerability relies upon:
a simple coding error-allowing untrusted input to be run as a command. In the current incarnation of the exploit, an attacker appends a valid command onto the end of the name of a directory using the ampersand character. A script with the coding error then reads the input and executes the command with administrator rights.
Seems if mankind can make it, mankind can also break it. Keep those systems patched, folks!
The US is about to finally embrace the secure chip-based authentication system called EMV-the standard was pioneered by Europay, MasterCard, and Visa-that the rest of the world has already adopted. Pushed by mounting fraud costs, credit card companies have crafted incentives for merchants to switch to the sophisticated readers needed to accept the cards. "There was a lot of skepticism about whether it would ever happen in the US," says Michael Misasi, an analyst with the Mercator Advisory Group. "All of the data breaches that have happened have woken people up, and progress has been accelerating this year." The first serious milestone is October 2015. By 2020 the swipe-and-sign magstripe reader will be as hard to find as the credit card impression rollers they supplanted.
The end is nigh for online credit card fraud, too. Systems like Apple Pay and
Visa's newly announced Visa Token Service (something Discover, Bank of America, Citibank and American Express offered several years earlier) accomplish the same security goals as EMV, but also work online. They replace the static credit card number with a temporary token that changes every time.
http://www.wired.com/2014/09/emv/Upgrade now, if you can.
A bug discovered in the widely used Bash command interpreter poses a critical security risk to Unix and Linux systems - and, thanks to their ubiquity, the internet at large.
From the Register:
It lands countless websites, servers, PCs, OS X Macs, various home routers, and more, in danger of hijacking by hackers.
The vulnerability is present in Bash up to and including version 4.3, and was discovered by Stephane Chazelas. It puts Apache web servers, in particular, at risk of compromise: CGI scripts that use or invoke Bash in any way - including any child processes spawned by the scripts - are vulnerable to remote-code injection. OpenSSH and some DHCP clients are also affected on machines that use Bash.
Now is also a good time to wipe your servers and reinstall Minix or Plan9 as a precaution. ;)
Imagine being able to chat with another user using what's in effect a modem program that transmits sounds at near ultrasonic frequencies. Now imagine your cat or dog being royally pissed off by your conversation.
The future is now. An anonymous Pipedotter wrote it to direct out attention to
quietnet, a program that does just that. It is a simple chat program that works without Wifi or Bluetooth connections and won't show up in a pcap. You need a good pair of speakers to make it work: If you can clearly hear the send script working then your speakers may not be high quality enough to produce sounds in the near ultrasonic range.
Quietnet is dependant on pyaudio[1] and Numpy[2].
[1]
http://people.csail.mit.edu/hubert/pyaudio/[2]
http://www.numpy.org/The same Anonymous Coward notes: "Quietnet is just a toy! Take a look at minimodem[3] or gnuradio[4] if you need something robust."
[3]
http://www.whence.com/minimodem/[4]
http://gnuradio.org/[Ed. note: looks pretty interesting. Time to test out my cat's audio frequency sensitivity, that fuzzy bastard.]
WikiLeaks has released previously unseen copies of weaponised German surveillance malware used by intelligence agencies around the world to spy on journalists, political dissidents and others."FinFisher (formerly part of the UK based Gamma Group International until late 2013) is a German company that produces and sells computer intrusion systems, software exploits and remote monitoring systems that are capable of intercepting communications and data from OS X, Windows and Linux computers as well as Android, iOS, BlackBerry, Symbian and Windows Mobile devices. FinFisher first came to public attention in December 2011 when WikiLeaks published documents detailing their products and business in the first SpyFiles release. ...
FinFisher continues to operate brazenly from Germany selling weaponised surveillance malware to some of the most abusive regimes in the world. The Merkel government pretends to be concerned about privacy, but its actions speak otherwise. Why does the Merkel government continue to protect FinFisher? This full data release will help the technical community build tools to protect people from FinFisher including by tracking down its command and control centers."
FinFisher Relay and FinSpy Proxy are the components of the FinFisher suite responsible for collecting the data acquired from the infected victims and delivering it to their controllers. It is commonly deployed by FinFisher's customers in strategic points around the world to route the collected data through an anonymizing chain, in order to disguise the identity of its operators and the real location of the final storage, which is instead operated by the FinSpy Master."
Let's go back in time to a couple of months ago when the German government was furious to learn the US had eavesdropped on Ms. Merkel's cellphone conversations. That anger looks a bit different now, mmmm?

How do you feel about the government maintaining a database of voice samples of everyone? If you're not against the practice, then Australia might be the place for you.
A
new voice recognition system in use by the Australian Tax Office (ATO) to identify customers. The system asks taxpayers to repeat a phrase in order to compare it to a voiceprint by which they can prove their identity.
The system is expected to save up to 45 seconds per phone call. The ATO receives about 8 million calls each year, 6 million of which require identification checks, for a total of about 3125 days, or 75,000 hours, each year spent performing identity checking.
On the one side, that's interesting tech, was probably a fun database project for some team, and saves money. What's not to like? On the other hand, you can bet that the NSA and similar agencies are also employing some version of this technology. So, who would like to step up to the microphone?
[Author note: On the flip side, it could be useful for people to record telemarketers so we can build a database of the people who spam us with annoying phone calls.]
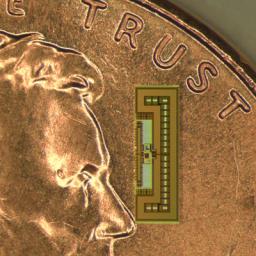
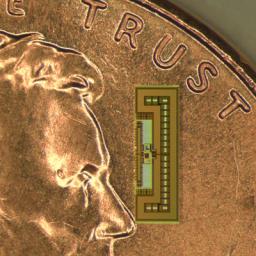 A Stanford engineering team has built a radio the size of an ant
A Stanford engineering team has built a radio the size of an ant, a device so energy efficient that it gathers all the power it needs from the same electromagnetic waves that carry signals to its receiving antenna - no batteries required.
Designed to compute, execute and relay commands, this tiny wireless chip costs pennies to fabricate - making it cheap enough to become the missing link between the Internet as we know it and the linked-together smart gadgets envisioned in the "Internet of Things." "The next exponential growth in connectivity will be connecting objects together and giving us remote control through the web," said Amin Arbabian, an assistant professor of electrical engineering who recently demonstrated this ant-sized radio chip at the VLSI Technology and Circuits Symposium in Hawaii.
Much of the infrastructure needed to enable us to control sensors and devices remotely already exists: We have the Internet to carry commands around the globe, and computers and smartphones to issue the commands. What's missing is a wireless controller cheap enough to so that it can be installed on any gadget anywhere. "How do you put a bi-directional wireless control system on every lightbulb?" Arbabian said. "By putting all the essential elements of a radio on a single chip that costs pennies to make."
Cost is critical because, as Arbabian observed, "We're ultimately talking about connecting trillions of devices."
This is amazing stuff. Check out the website for pictures of the radio, which is smaller than Lincoln's forehead on an American penny, as well as links to the developers' website with more musings on the future of gadgets that remain connected and controllable.
There's a good editorial over at ZDNet by
Violet Blue, who writes in the "Zero Day" opinion column:
Wake up: The celebrity nudes hack is everyone's problem. The celebrity nudes 'hacking' scandal is a wake up call about security and human nature.The amount of private data theft going on right now is insane. Until the online revolution, our private spaces were our bedrooms and bathrooms, our homes, sex clubs, our phone calls and our inner fantasy worlds. Now, our private spaces for adult playtime include texts, emails and direct messages to trusted friends or family members, and especially photos. But that's only true if we really trust the person we share them with.
The problem we face now is that not everyone understands or agrees what constitutes a private space online. Online, private spaces include our email inboxes, chat rooms, IRC, social media profiles and their not-public messaging systems (Twitter DMs, Facebook chat), dating websites, message boards. Private space now includes all the places that our personal information resides.
I have an alternate theory, though I do agree with Violet Blue: maybe
Web 2.0 and the "culture of sharing" is the problem? Web 1.0 wasn't so bad, if you ask me.