What does GCHQ know about our devices that we don't?
 While the initial disclosures by Edward Snowden revealed how US authorities are conducting mass surveillance on the world's communications, further reporting by the Guardian newspaper uncovered that UK intelligence services were just as involved in this global spying apparatus. Faced with the prospect of further public scrutiny and accountability, the UK Government gave the Guardian newspaper an ultimatum: hand over the classified documents or destroy them. The Guardian decided that having the documents destroyed was the best option.
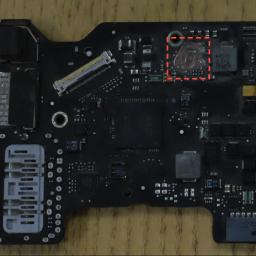
While the initial disclosures by Edward Snowden revealed how US authorities are conducting mass surveillance on the world's communications, further reporting by the Guardian newspaper uncovered that UK intelligence services were just as involved in this global spying apparatus. Faced with the prospect of further public scrutiny and accountability, the UK Government gave the Guardian newspaper an ultimatum: hand over the classified documents or destroy them. The Guardian decided that having the documents destroyed was the best option.That's the beginning of the story, not the end of it, and it gets more troubling as you read on. Have a look at this article over at Privacy International [ed. note: an oxymoron if there ever were one] and find out that the UK's security services had an unnatural interest in keyboards and certain components of modern, mobile telephone technology.
Any questions? Just call.