Garmin global outage caused by ransomware attack, sources say
An ongoing global outage at sport and fitness tech giant Garmin was caused by a ransomware attack, according to two sources with direct knowledge of the incident.
The incident began late Wednesday and continued through the weekend, causing disruption to the company's online services for millions of users, including Garmin Connect, which syncs user activity and data to the cloud and other devices. The attack also took down flyGarmin, its aviation navigation and route-planning service.
Portions of Garmin's website were also offline at the time of writing.
Garmin has said little about the incident so far. A banner on its website reads: We are currently experiencing an outage that affects Garmin.com and Garmin Connect. This outage also affects our call centers, and we are currently unable to receive any calls, emails or online chats. We are working to resolve this issue as quickly as possible and apologize for this inconvenience."
In a brief update on Saturday, Garmin said it had no indication that this outage has affected your data, including activity, payment or other personal information."
The two sources, who spoke on the condition of anonymity as they are not authorized to speak to the press, told TechCrunch that Garmin was trying to bring its network back online after the ransomware attack. One of the sources confirmed that the WastedLocker ransomware was to blame for the outage.
One other news outlet appeared to confirm that the outage was caused by WastedLocker.
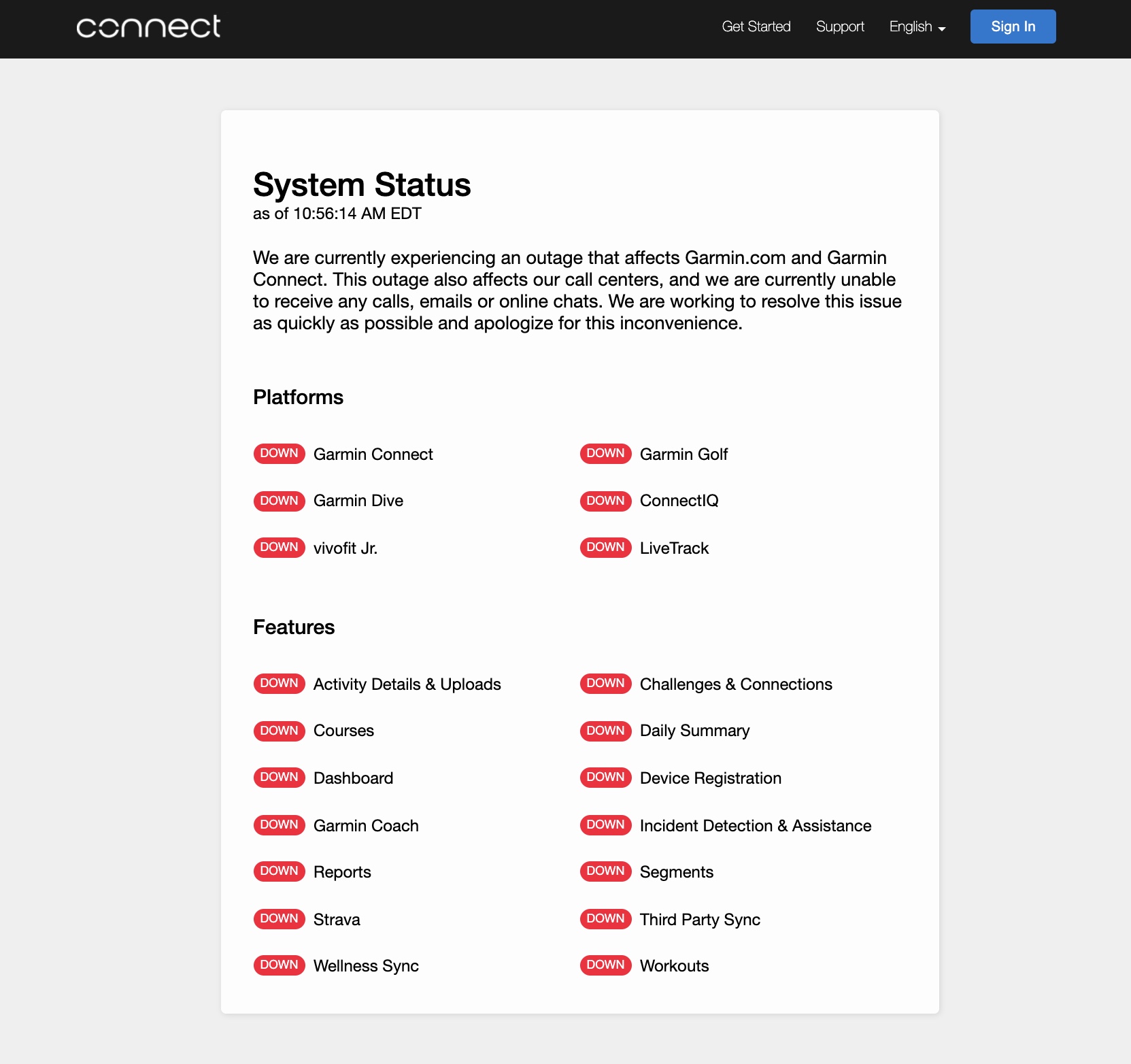
Garmin's online services have been down for days. The cause is believed to be ransomware, according to two sources with direct knowledge of the incident. (Screenshot: TechCrunch)
WastedLocker is a new kind of ransomware, detailed by security researchers at Malwarebytes in May, operated by a hacker group known as Evil Corp. Like other file-encrypting malware, WastedLocker infects computers, and locks the user's files in exchange for a ransom, typically demanded in cryptocurrency.
Malwarebytes said that WastedLocker does not yet appear to have the capability to steal or exfiltrate data before encrypting the victim's files, unlike other, newer ransomware strains. That means companies with backups may be able to escape paying the ransom. But companies without backups have faced ransom demands as much as $10 million.
The FBI has also long discouraged victims from paying ransoms related to malware attacks.
Evil Corp has a long history of malware and ransomware attacks. The group, allegedly led by a Russian national Maksim Yakubets, is known to have used Dridex, a powerful password-stealing malware that was used to steal more than $100 million from hundreds of banks over the past decade. Later, Dridex was also used as a way to deliver ransomware.
Yakubets, who remains at large, was indicted by the Justice Department last year for his alleged part in the group's unimaginable" amount of cybercrime during the past decade, according to U.S. prosecutors.
The Treasury also imposed sanctions on Evil Corp, including Yakubets and two other alleged members, for their involvement in the decade-long hacking campaign.
By imposing sanctions, it's near-impossible for U.S.-based companies to pay the ransom - even if they wanted to - as U.S. nationals are generally prohibited from engaging in transactions with them," per a Treasury statement.
Brett Callow, a threat analyst and ransomware expert at security firm Emsisoft, said those sanctions make it especially complicated" for U.S.-based companies dealing with WastedLocker infections.
WastedLocker has been attributed by some security companies to Evil Corp, and the known members of Evil Corp - which purportedly has loose connections to the Russian government - have been sanctioned by the U.S. Treasury," said Callow. As a result of those sanctions, U.S persons are generally prohibited from transacting with those known members. This would seem to create a legal minefield for any company which may be considering paying a WastedLocker ransom," he said.
Efforts to contact the alleged hackers were unsuccessful. The group uses different email addresses in each ransom note. We sent an email to two known email addresses associated with a previous WastedLocker incident, but did not hear back.
A Garmin spokesperson could not be reached for comment by phone or email on Saturday. (Garmin's email servers have been down since the start of the incident.) Messages sent over Twitter were also not returned. We'll update if we hear back.
As ransomware gets craftier, companies must start thinking creatively
Send tips securely over Signal and WhatsApp to +1 646-755-8849, or email: zack.whittaker@protonmail.com