If you're using
TAILS, or just interested in the technology, or even thinking about getting on board, here is some good news for you:
the TAILS has opened an official public mailing list with archives. You can find the new mailing lists at
tails-project@boum.org, which is a public, archived mailing-list to talk about the non-technical decisions regarding the project. In addition the page mentions two other new mailing lists, but they are not aimed directly at TAILS users, but for promotion and web/soft/UI. Click on the "mailing list" [1] link to browse the TAILS USERS Mailing List archives.
More here:
https://mailman.boum.org/listinfo/tails-projectI personally have to manage upwards of 180 passwords on a regular basis and lots of folks deal with more than that. Sure, you can simplify by reusing passwords, but common sense says that's a bad idea. But better systems inevitable require you manage them in a password app or equivalent, which opens another vulnerability, as cracking that data store can net a crook your entire password collection. Clearly, there's progress to be made here.
The reported theft of 1.2 billion email passwords by Russian hackers earlier this month was just the latest in a long string of major password security breaches that have led some people to wonder if the use of passwords should be abandoned.
But given recent breaches of systems and so on, the BBC is asking the inevitable question, which is
has the flawed password system finally reached its end, and if so, what will replace it? Check out their review of alternatives, including digital portraits, voice recognition, and more.
What about Pipedotters: how do you manage your passwords, and which direction makes sense for this not-evolving-fast-enough technology?
Tails was compromised, and everyone is wondering what is going to happen next. But a team of researchers in Canada hopes they have the answer:
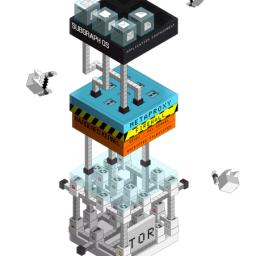
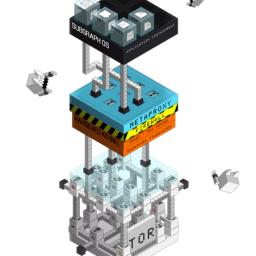
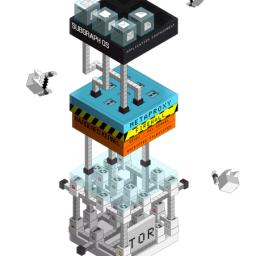
Subgraph, an operating system resistant to zero-day exploits.
In Subgraph OS, any application a computer interacts with running the operating system is isolated in containers to prevent exploits from having a meaningful impact at the OS level. It uses the Grsecurity kernel, a patch applied to the Linux kernel that enhances security by limiting what processes can do. For example, with most operating systems, receiving an infected PDF making use of a zero-day vulnerability means before you realize it, there's malicious code running on your computer. ... he new OS is also, obviously, designed for complete anonymity. All the connections in the OS are intercepted by a metaproxy that then routes them through Tor. The metaproxy has some nifty tricks, too: it opens different Tor circuits for different apps, to avoid an attacker correlating traffic to the same origin.
Subgraph is based on Debian, PGP, and other open source technologies and products.
"Spooks have called upon the good people of Blighty to help protect an airline from attack by a vicious group of nerdy cyber-terrorists. That might sound like the secret services are getting a bit desperate, but don't worry kids: it's only a game.
The bods at GCHQ have announced a new part of the Cyber Security Challenge UK designed to unearth potential digital knights of the realm.
If you think you've got the stuff, and haven't read "Enders Game" so that the irony would interfere with your sense of patriotism,
have a look!
BitTorrent Bleep expands the Bittorent protocol to enable people to make voice calls and send messages over the Internet without using a central server to direct traffic. Users will find one another through groups of other users, with no records of the calls or texts stored anywhere along the way. Once a connection is made for a call or text, the communication travels directly between the two computers involved. That peer-to-peer approach also defies mass surveillance.
BT Bleep is currently invitation only and limited to Windows 7 and 8.
An
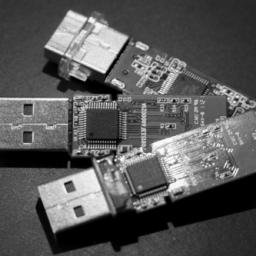
interesting discussion appeared on
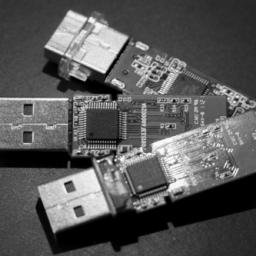
MacRumors today pointing to the work of security researcher Karsten Nohl of Berlin's
SR Labs. He has discovered an attack vector exploiting the firmware of generic USB devices. It appears that with the vector involves reprogramming the USB controller software for arbitrary devices which can than emulate other devices to cause a large variety of undesired outcomes (such as emulating a keyboard to type on behalf of a user or spoofing a network card and redirecting web traffic). At present, this attack vector appears to be impossible to prevent or detect with existing software-only security measures. A more detailed discussion of Nohl's work and the associated risk are
available from Wired or the
SR Labs website itself.
A notable quote from the Wired article:
"Blaze speculates that the USB attack may in fact already be common practice for the NSA. He points to a spying device known as Cottonmouth, revealed earlier this year in the leaks of Edward Snowden. The device, which hid in a USB peripheral plug, was advertised in a collection of NSA internal documents as surreptitiously installing malware on a target's machine. The exact mechanism for that USB attack wasn't described. I wouldn't be surprised if some of the things [Nohl and Lell] discovered are what we heard about in the NSA catalogue....The alternative is to treat USB devices like hypodermic needles."
The Tor network has published the following advisory on the tor-announce mailing list:
SUMMARY
On July 4 2014 we found a group of relays that we assume were trying to deanonymize users. They appear to have been targeting people who operate or access Tor hidden services. The attack involved modifying Tor protocol headers to do traffic confirmation attacks.
The attacking relays joined the network on January 30 2014, and we removed them from the network on July 4. While we don't know when they started doing the attack, users who operated or accessed hidden services from early February through July 4 should assume they were affected.
The Tor folks confess it's still unclear what "affected" includes:
We know the attack looked for users who fetched hidden service descriptors, but the attackers likely were not able to see any application-level traffic (e.g. what pages were loaded or even whether users visited the hidden service they looked up). The attack probably also tried to learn who published hidden service descriptors, which would allow the attackers to learn the location of that hidden service. In theory the attack could also be used to link users to their destinations on normal Tor circuits too, but we found no evidence that the attackers operated any exit relays, making this attack less likely. And finally, we don't know how much data the attackers kept, and due to the way the attack was deployed (more details below), their protocol header modifications might have aided other attackers in deanonymizing users too.
Relays should upgrade to a recent Tor release (0.2.4.23 or 0.2.5.6-alpha), to close the particular protocol vulnerability the attackers used - but remember that preventing traffic confirmation in general remains an open research problem. Clients that upgrade (once new Tor Browser releases are ready) will take another step towards limiting the number of entry guards that are in a position to see their traffic, thus reducing the damage from future attacks like this one. Hidden service operators should consider changing the location of their hidden service."
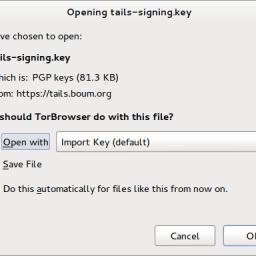 Tails, The Amnesic Incognito Live System, version 1.1.1, is out.
Tails, The Amnesic Incognito Live System, version 1.1.1, is out.