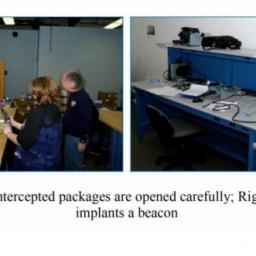
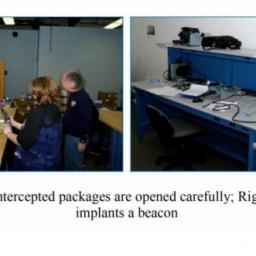
Here's how the NSA is doing its part to sink the American tech sector by ensuring no one ever buys American products anymore. Ars Technica reports
the NSA is intercepting hardware and implanting its backdoors ("beacons") before they are rerouted back to the original destination - the customer. This quote is taken from
Glenn Greenwald's No Place to Hide book detailing his investigations and Snowden's allegations. The statement was made by an NSA rep:
Here's how it works: shipments of computer network devices (servers, routers, etc,) being delivered to our targets throughout the world are intercepted. Next, they are redirected to a secret location where Tailored Access Operations/Access Operations (AO-S326) employees, with the support of the Remote Operations Center (S321), enable the installation of beacon implants directly into our targets' electronic devices. These devices are then re-packaged and placed back into transit to the original destination. All of this happens with the support of Intelligence Community partners and the technical wizards in TAO.
Already, most of the world has decided that storing data on American servers or using American service providers is a risk. Thanks, NSA, for making sure no one buys American hardware either.

In the words of the Register, "see if this sounds familiar."
Not good times for the Dogecoin wallet provider DogeVault. This isn't news hot-off-the-press:
Dogevault went offline on May 13th .
They are hoping their backups work as they attempt to restore service. But who cares? Pundits are already singing their
dirge for Dogecoin , or calling it
doomed to failure .
So: what's next? Dogecoin was a fluke, right? A mirthful riff on the success of Bitcoin, that by luck or happenstance wound up becoming temporarily worth something? If you believe cryptocurrencies are the future, what's the plan, if hacks and wallet thefts become the almost unstoppable future? Or if you believe cryptocurrencies are a passing nerd fad, what comes next?
This just in from the Register: If you're watching a "smart television" containing internet capability and camera/microphone,
your television is also watching you and can be coopted via malware to do all sorts of terrible things. Manufacturers seem to be blind to this, turning out lots of new models of internet-aware devices that risk being "smart" in all the wrong ways.
[Security experts] demonstrated exactly [the vulnerability] just down the road from the Infosec Europe conference, held in London. "Installing the bugging software requires physical access to the device, which is how we did it, or by installing a malicious app," said Felix Ingram, principal consultant at NCC Group. "Malicious apps could be downloaded from the manufacturer's app store. The TV does have the option for auto-updating, so releasing a legitimate app, then releasing a malicious update, is another attack vector."
Why bother buying a Smart TV though, when you can
much more simply make your own using a Raspberry Pi [video]? You control the hardware, you control the software, and for bonus points you don't have to rely on the manufacturer to provide you the occasional firmware update out of the goodness of their hearts.
On May 13 and May 20, 2014, PBS FRONTLINE will air a two-part series entitled
United States of Secrets , detailing the
"inside story of the U.S. government's massive and controversial secret surveillance program." "Through in-depth interviews with more than 60 whistleblowers, elected officials, journalists, intelligence insiders and cabinet officials, we have woven together the secret narrative that reveals the scale and scope of the government's spying program," says Kirk. "We've gone deep inside the story, from what really happened at the NSA and the White House in the days after 9/11, through the Bush and Obama administrations, directly into the stunning revelations from Edward Snowden."
Part one, which will broadcast as a two-hour episode May 13 at 9pm on PBS, will cover the history of the NSA surveillance program from its beginnings following the events of September 11 to the present day. Part two will explore the secret relationship between Silicon Valley and the NSA, and will be shown May 20 at 10pm on PBS. Check your
local listings .
In the Snowden era, it's pretty clear that the Internet as a worldwide communication medium that would permit activists to securely communicate and disseminate information has not been effective:
governments appear to be surprisingly and increasingly effective at clamping down on, censoring, controlling Internet information
as well as using it to track down dissidents. Mobile telephony isn't much better as it's a related technology that suffers many of the same ills as TCP/IP with regard to anonymity. So the privacy gurus are turning to a technology you'd probably forgotten:
Ham Radio .
Airchat, they call it, and
it's got a few characteristics that make it very interesting and useful . The group states:
The goal of the project is to communicate directly, without using Internet or cellular infrastructure. ... We traded bandwidth for freedom, simplicity and low cost.
It's not a fast protocol, since packet data over audio channels is necessarily low bandwidth. But its promise to offer real anonymity is a big deal. And not surprisingly, these enterprising hackers are having fun with it. For starters, to anonymise communications and handle encryption and error correction, the system uses a packet they call
the Lulzpacket .
Curious?
go check out the code for yourself on github .
From the
OpenBSD Journal and the
release page :
As you can now easily tell from the OpenBSD main web site, OpenBSD 5.5 has been released.
Looking at the
release announcement and other sources such as the
release page , it's easy to see that there are numerous goodies in store for you:
- A whole new traffic shaping system to replace ALTQ
- Cryptographically signed base sets and packages
- Automatic installation features
- Improved hardware support, and more
Also, from OpenBSD 5.5 onwards, OpenBSD is year 2038 ready and will run well beyond Tue Jan 19 03:14:07 2038 UTC. The entire source tree (kernel, libraries, and userland programs) has been carefully and comprehensively audited to support 64-bit time_t.
A very recent
firmware analysis from the reverse engineer Eloi Vanderbeken shows that NETGEAR didn't fix the backdoor on port 32764 but instead implemented a knocking feature that is now required to unlock the service.
Summary from the slides: The knocking feature is initiated when a "packet type == 0x201" arrived at "ft_tool" that listens to the Ethernet packets. It only works with EtherType 0x8888 and the payload has to be "45d1bb339b07a6618b2114dbc0d7783e" which is the MD5-hash of the model number DGN1000. If such a packet arrives, the backdoor service /usr/bin/scfgmgr f- is launched.
Ars Technica reports :
The nature of the change, which leverages the same code as was used in the old firmware to provide administrative access over the concealed port, suggests that the backdoor is an intentional feature of the firmware and not just a mistake made in coding. "It's DELIBERATE," Vanderbecken asserted in his presentation.
(Cross posted on Soylentnews)Here's a little something to sour your morning coffee with the acid taste of anxiety:
an interesting piece by Joanna Rutkowska pointing out what she claims is an inherent security flaw in the
X Window GUI model :
... Start another terminal window, and switch to root (e.g. using su, or sudo). Notice how the xinput running as user is able to sniff all your keystrokes, including root password (for su), and then all the keystrokes you enter in your root session. Start some GUI app as root, or as different user, again notice how your xinput can sniff all the keystrokes you enter to this other app!
I never knew this and am not aware of much discussion going on about the issue. Is this a fundamental flaw that Windows Vista addresses more successfully, as the author claims, or has the time truly come to do away with the X Window model and develop something else? Did
the UNIX-Haters Handbook get this one right?
Back in October 2013,
Kenneth White and Matthew Green kicked off the idea to do a full and complete audit of TrueCrypt, the most popular disk encryption package out there. They raised over $60,000 dollars and 33BTC to this end, and got underway.
The first part of the audit - the in-depth source code review - was performed by a security firm and completed on April 14 of this year (
report ).
The results are interesting to read. No bogeys have been found so far, though 11 medium-to-minor items were identified. But the authors did note:
Overall, the source code for both the bootloader and the Windows kernel driver did not meet expected standards for secure code. This includes issues such as lack of comments, use of inse-cure or deprecated functions, inconsistent variable types, and so forth.
The next stage,
cryptanalysis , has begun and is proceeding.
I'm sure plenty of people are thinking, "How about doing the same thing for OpenSSL?" I'd personally prefer to see this sort of effort going into improving the OpenSSL software.
A remote vulnerability in the OpenSSL library was disclosed yesterday. A missing bounds check in the Heartbeat Extension implementation can trigger a buffer over-read leading to the loss of sensitive data, including the disclosure of the private key.
The Heartbleed bug allows anyone on the Internet to read the memory of the systems protected by the vulnerable versions of the OpenSSL software. This compromises the secret keys used to identify the service providers and to encrypt the traffic, the names and passwords of the users and the actual content. This allows attackers to eavesdrop on communications, steal data directly from the services and users and to impersonate services and users.
More information:
 Here's how the NSA is doing its part to sink the American tech sector by ensuring no one ever buys American products anymore. Ars Technica reports the NSA is intercepting hardware and implanting its backdoors ("beacons") before they are rerouted back to the original destination - the customer. This quote is taken from Glenn Greenwald's No Place to Hide book detailing his investigations and Snowden's allegations. The statement was made by an NSA rep:
Here's how the NSA is doing its part to sink the American tech sector by ensuring no one ever buys American products anymore. Ars Technica reports the NSA is intercepting hardware and implanting its backdoors ("beacons") before they are rerouted back to the original destination - the customer. This quote is taken from Glenn Greenwald's No Place to Hide book detailing his investigations and Snowden's allegations. The statement was made by an NSA rep: