Update Zoom for Mac now to avoid root-access vulnerability

Enlarge / A critical vulnerability in Zoom for Mac OS allowed unauthorized users to downgrade Zoom or even gain root access. It has been fixed, and users should update now. (credit: Getty Images)
If you're using Zoom on a Mac, it's time for a manual update. The video conferencing software's latest update fixes an auto-update vulnerability that could have allowed malicious programs to use its elevated installing powers, granting escalated privileges and control of the system.
The vulnerability was first discovered by Patrick Wardle, founder of the Objective-See Foundation, a nonprofit Mac OS security group. Wardle detailed in a talk at Def Con last week how Zoom's installer asks for a user password when installing or uninstalling, but its auto-update function, enabled by default, doesn't need one. Wardle found that Zoom's updater is owned by and runs as the root user.
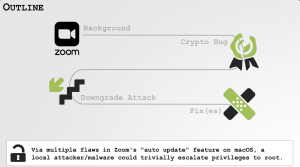
It seemed secure, as only Zoom clients could connect to the privileged daemon, and only packages signed by Zoom could be extracted. The problem is that by simply passing the verification checker the name of the package it was looking for ("Zoom Video ... Certification Authority Apple Root CA.pkg"), this check could be bypassed. That meant malicious actors could force Zoom to downgrade to a buggier, less-secure version or even pass it an entirely different package that could give them root access to the system.