 |
by Lyle Seaman on (#763S9)
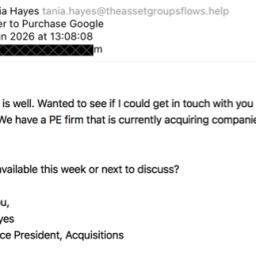
"Scammer offers to buy Google" is certainly a new twist on a very old New York con.Jan B. explains"Scammers have found a new way to steal money, scrapLinkedIn profiles and then send out emails with fake offersto buy people's companies. I'm guessing suddenly they need somefees paid just before the deal is finalised. However, theymay need to improve their filtering before sending out theirscams, I don't even own Google!" I'm putting together a group of peopleto buy it, do you want to get in the deal? I'll just need you to transfertwo million to this SWIFT account...
|
 The Daily WTF
The Daily WTF
| Link | http://thedailywtf.com/ |
| Feed | http://syndication.thedailywtf.com/TheDailyWtf |
| Updated | 2026-06-08 09:00 |
 |
by Remy Porter on (#7630K)
If there's one thing that seems to be a constant source of issues, it's people constructing SQL queries through string concatenation. Even if you're using parameters in the query, I'm opposed to handling raw SQL as strings in my programs. My solution is always "use a builder"- an API that constructs a syntax tree that it can then render to SQL as needed. (Yes, a builder, not an ORM, that's a whole other discussion, I'm not dogmatically anti-ORM, but it's a leaky abstraction at best.)Many languages have such a thing, Java included. Lukasz's team was using Java, and they had a rule: "don't do SQL strings, use a builder". Unfortunately for Lukasz's team, their guideline didn't specify what kind of builder.
|
 |
by Remy Porter on (#7629E)
Frank suspected something odd when he spotted a use of React's useMemo function in some JavaScript code. Now, there's nothing wrong with using that method, in and of itself. It watches some variables and recalculates a callback if they change for any reason. It's a great tool for when you want to avoid recalculating expensive things over and over again.But in this case, the calculation in question was isAuthorized, which wasn't an expensive calculation; it was just checking if certain values are set. The code looked like this:
|
 |
by Remy Porter on (#761EC)
Volodya sends us some bad date handling code in PHP. Which, I know, you're just reaching for the close tab and yawning when you hear that. You've seen it before. But bear with me, this one still has some fun bits to it.
|
 |
by Ellis Morning on (#760MR)
The real WTF is that our long-time friend and submitter Argle failed to dissuade all three of his sons from pursuing IT careers of their own:
|
 |
by Lyle Seaman on (#75YTA)
It's ironic -- this site gets absolutely inundated with blogspam from people trying to improve their SEO ranking, and yet the only requirement to get your website linked is one dumb little typo in the right menu.Faithful Michael R. is still job hunting, now even farther afield."I shall try the gigs in United Kingsom. https://electronicmusicopenmic.com/"
|
 |
by Remy Porter on (#75XYZ)
Untodesu sends us this submission, with this comment:
|
 |
by Remy Porter on (#75X3J)
Are there any files to send? That's the question that Chris C's predecessor had. So they asked it. Again. And again. And again.Chris writes:
|
 |
by Ellis Morning on (#75WBJ)
The waters are even more dangerous than we imagined. Have a look at some of the crazed whales our brave submitters and commenters have encountered in the wild.First comes an Anonymous tale of woe:
|
 |
by Jake Vinson on (#75VQC)
|
 |
by Lyle Seaman on (#75T23)
"April is special," writesElwin. It is, but take heart May, every month is special at TDWTF.
|
 |
by Remy Porter on (#75S66)
Delilah works in a Python shop. Despite Python's "batteries included" design, that doesn't stop people from trying to make their own batteries from potatoes. For example, her co-worker wrote this function:
|
 |
by Remy Porter on (#75RCF)
A depressing quantity of software is what I would call a "data pump". I have some data over here, and I need it over there. Maybe I'm integrating into a legacy app. Or into an ERP. Or into a 3rd party API. At the end of the day, I have data in one place, and I want it in another place.Sally has a Java application written in the Quarkus framework, which has a nightly batch that works to keep a table of Bar entities in sync with a table of Foo entities. (This anonymization comes from Sally) These exist in the same database. There is also a Bar webservice, which provides information about the Bar entities. The workflow, such as it is, is that the software needs to find all of the Foo entities that do not currently have associated Bar entities, and then call the Bar webservice to get the required information to create those Bar entities.Let's see how that works.
|
 |
by Remy Porter on (#75QEG)
JB has a database table that, at first glance, looks like one of those data warehouse tables that exists to make queries performant. You know the sort, the table that contains every date between 1979 and 2050, or every number out to 1,000,000 or something. It looks dumb, but it helps make certain joins and queries performant.The database table is called three_alpha_numerics. It has two columns: digit, which contains three characters, and is_numeric, which is a a single character: 'Y' or 'N'. It looks roughly like this:
|
 |
by Remy Porter on (#75PKS)
Another representative line, and this one comes from an Excel spreadsheet. But, per Remy's Law of Requirements gathering ("No matter what the requirements doc says, what your users wanted was Excel"), this one was actually written by a developer. A developer who didn't understand how Excel works, but more important, didn't understand how dates worked either.This comes from Ulysse J.
|
 |
by Lyle Seaman on (#75MYC)
"Winner ad placement!" snarked our Peter G.
|
 |
by Ellis Morning on (#75M0E)
Jani, a master's student of bioinformatics, was seated near the back of a large classroom. This was a simple compulsory elective course geared toward biologists. The professor was currently walking the class through their latest assignment. "We'll need to connect to some Linux servers," he announced.The other students seated nearby traded blank stares. They were all Mac and Windows users with no IT background. Meanwhile Jani, a veteran Linux user, started feeling a little smug. An easy A was at hand."First," the professor continued, "you'll need a private key."After the professor had explained a few details, the first WTF came in the form of a bulk email sent to the entire class. The private key was attached. The username was the email address it was sent to.What do you call the exact opposite of a private key? Jani wondered, bemused."You'll also need to download an application to help you log in," the professor said. "I recommend MobaXterm."As he detailed the process of visiting the SSH client website to download the software, Jani tuned out. He didn't need such hand-holding. He accessed OpenSSH, tried connecting ...... and failed.Meanwhile, everyone around him was logging in no problem.Jani's face burned with embarrassment at this second WTF. His first instinct was to blame the deprecated cryptography of the server. He spent most of the remaining lecture time searching for a way to allow his SSH to use SSH-DSS. (It turned out to be supported the whole time, despite the warnings he received.)Jani then tried to re-download the "private" key and adjust the SSH config file several times. He cycled through different possible usernames associated with his university email account.No dice.He was the only person in the class who hadn't yet logged into the server. Not even the professor was able to help him, since he was using Linux.Embarrassment and frustration mounted. An hour later, out of ideas, Jani fell back to downloading MobaXterm and running it inside Wine.It didn't work. The professor offered him a spare Windows box. "Here, try this one."Jani booted it up, copied the "private" key to the new machine ... and still couldn't sign in.Now, this was getting suspicious.The lecture ended. A friend of Jani's hung back while the rest of the students filed out. "Why don't you try logging in with my credentials instead of yours?" she asked.Jani was up for anything at that point.It worked. On his own machine, on the Windows box, everywhere.With that lead in mind, Jani opened the server's /etc/passwd file to look at all the usernames. He noticed that, unlike everyone else, his username and email address didn't match.His university used Microsoft emails. Everyone had several address aliases, and they could also use whatever email address they liked in the system, even a personal one.Jani had chosen to use a school email in the form of <number>@uni.uni. Unfortunately, the Ubuntu server didn't like the idea of user being named just <number>, so it had renamed it to user<number>. Some script for generating SSH configuration had probably failed from there, because Jani also discovered that his user home directory was missing a .ssh directory and known_hosts file.Unfortunately, due to restricted access, he wasn't able to copy them from any of his classmates. In the end, he could connect to the server as any of his classmates, but not as himself.[Advertisement] Picking up NuGet is easy. Getting good at it takes time. Download our guide to learn the best practice of NuGet for the Enterprise.
|
 |
by Remy Porter on (#75K8C)
Today's anonymous submitter sends us two blocks. The first is a perfectly normal line of React code:
|
 |
by Remy Porter on (#75JD3)
Frequent submitter Argle (previously), sends us a short little representative line. The good news is that this line of code came across Argle's screen during a code review: it was being removed. The bad news is that it was sitting in the code base for ages.
|
 |
by Remy Porter on (#75HKF)
Today's anonymous submitter works for a large company. It's one of those sorts of companies which has piles, and piles, and piles of paperwork and bureaucracy. It also means that much of their portfolio of software is basic CRUD applications. "Here's a database for managing invoices." "Here's a database for managing desk assignments." "Here's a pile of databases which link our legacy applications to our new ERP system."Which brings us to our representative line. It is not a representative line of code, but a representative line of the design specification. This is the design specification for yet another database-driven application.
|
 |
by Lyle Seaman on (#75FXR)
The single most common category of entries for this column is failed handling of NaN, null and undefined. Almost exclusively from javascript in web pages, sometimes in node servers, and almost never any other languages or frameworks. They're getting a bit repetitive but it's our solemn duty to call out failure where we find it. So if you send us one of these, make sure it identifies the source!"If you want something you've never had, do something you'venever done" exhorted Ben.
|
 |
by Remy Porter on (#75F59)
Russell F (previously) sends us a small one today. It's not just a representative line, it's a representative comment. More than that, it's a true confession. Russell wrote some code, you see, and the logic was confusing. So, a co-worker added a comment to explain what the code was doing:
|
 |
by Remy Porter on (#75EAS)
As previously discussed, C++ took a surprisingly long time to get a "starts with" function for strings. It took even longer to get a function called "contains". In part, that's simply because string::find solves that problem.Nancy sends us a... different approach to solving this problem.
|
 |
by Remy Porter on (#75DGD)
Today's anonymous submitter sends us some code that just makes your mind go... blank when you look at it.
|
 |
by Remy Porter on (#75CRK)
If you've seen one developer recounting how their AI agent deleted production, you've seen them all. They're mostly not interesting stories. It's like watching someone speeding through traffic on a motorcycle without a helmet: the eventual tragedy is sad, but it's unsurprising and not an interesting story to tell. It's not even interesting as a warning: the kind of person who speeds on a motorcycle without a helmet isn't doing so because they don't understand the danger. They've just decided it doesn't apply to them.But the founder of PocketOS, Jer, recently shared how- whoopsie!- their AI agent deleted production. There's a lot of ingredients that go into this particular disaster, which I think makes it interesting, because the use of a poorly supervised AI agent is only one ingredient in this absolute trainwreck of a story.PocketOS is a small company that makes software for rental companies to manage reservations. Car rentals are a big customer, but the tool is more general than that. They manage all of their infrastructure via a service called Railway. Railway is a pretty-looking GUI tool for automating your deployments and the target environments.PocketOS also is heavily adopting Cursor wrapping around the Claude model. They've paid big bucks for the top-end model offered. Many of their components, like Railway, offer MCP services so that their LLM can do useful things. They're using the Claude LLM to automate as much as they can.So far, this is all a pretty typical setup. They pointed Claude at their code and gave it a "routine" task, and sent it to work. It toddled through the problem and encountered a credential issue. It "decided" that the fix for this issue was to delete a storage volume and recreate it. It scanned through the code to find a file containing an API key, found it, and then sent a POST request via cURL to delete the volume in question.Jer writes:
|
 |
by Lyle Seaman on (#75B6C)
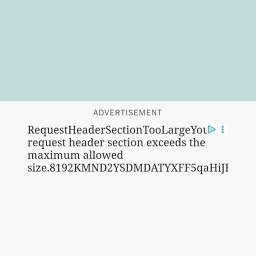
Roger C. gets on second base with an unforced error. "Not only is the content too large, the error message informing us of this is also too large to fit the visible space. A layered, double WTF."
|
 |
by Remy Porter on (#75ABN)
"This WTF is in Matlab" almost feels like cheating. At one place I worked, somebody's job was struggling through a mountain of Matlab code and porting it into C. "This Matlab code looks like it was written by an alien," also doesn't really get much traction- all Matlab code looks like it was written by an alien. This falls into the realm of "Researchers use Matlab, researchers may be very smart about their domain, but generally don't know the first thing about writing maintainable code, because that's not their job."But let's take a look at some MatLab Carl W found:
|
 |
 |
by Remy Porter on (#758MM)
A few years back, C# added the concept of "primary constructors". Instead of declaring the storage for class members and then initializing them in the constructor, you can annotate the class itself with the required fields, and C# automatically generates a constructor for you. It's all very TypeScript and very Microsoft, and certainly cuts down on some boilerplate.Esben B's team isn't really using them in many places, but they are using a linter which is opinionated about them. So this in-line constructor causes the linter to complain:
|
 |
by Remy Porter on (#757T6)
We rip on PHP a lot, but I am willing to admit that the language and ecosystem have evolved over the years. What started as an ugly templating language is now just an ugly regular language.But what happens when you still really want to do things with templates? Allison has inherited a Python-based, WSGI application which rejects any sort of formal routing or basic web development best practices. Their way of routing requests is simply long chains of "if condition then invokeA elif otherCondition then invokeB". Sometimes, those conditions will directly set the MIME type on the HTTP response.They do use a templating library called Mako for generating their responses. They use it for their HTML responses, obviously. They also use it for their JSON responses, generating code like this:
|
by Lyle Seaman on (#755ZR)
"RFC 1738 (and 3986) disagree" and so doesDaniel D."Reddit API has some weird app creation going on withlots of recently migrated and undocumented stuff. But having redirectURL set to localhost (or 127.0.0.1) usually works. Well, ifyou don't disagree with Sir Tim Berners-Lee about what URLis. Which Reddit does. hostnumber = digits "." digits "."digits "." digits". I'd file this one with all the websites that try to perform validation on email addresses, and get it wrong.
 |
by Remy Porter on (#7552Q)
Henrik H (previously) sends us a simple representative C# line:
|
 |
by Remy Porter on (#7545Y)
Today, we look at a representative comment, sent to us by Nona. This particular comment was in a pile of code delivered by an offshore team.
|
 |
by Remy Porter on (#7539W)
Eric O worked for a medical device company. The medical device industry moves slowly, relative to other technical industries. Medical science and safety have their own cadence, and at a certain point, iterating faster doesn't matter much.Eric was working on a new feature on a system that had been in use for thirteen years. This new feature interacted with a database which stored information about racks of test tubes, and Eric's tests meant creating several entries for racks of test tubes. And that's when Eric discovered that the database only allowed thirty racks. Add any more, it would just roll right back over to one.This was odd. The database was small- less than 40MB, even in production- and there were automatic tasks to purge old data for compliance purposes. Why a hard limit of thirty?Eric had only been at the company for a year, so he asked one of the more senior team members, Lester. "Oh yeah, that was before my time. You should probably ask Carl."Later that day, Eric happened to bump into Carl around the coffee maker, and asked the question. "Oh, yeah, I do vaguely remember something about that. It was in the requirements for the product. I thought it was weird, but didn't think too much about it. You should probably ask Elise, she's been here like twenty years."Well, now it was getting curious. Eric went over to the "old building", as it was named, the original office for the company on the other side of the parking lot. Most of the offices had moved to the new building a decade earlier, and it mostly served as fabrication and storage, but a few offices remained.Elise was on the third floor, down a poorly lit hallway, sitting in an office with water-stained acoustical tile in its ceiling. "Oh, yeah, I put that into the requirements document. It's funny, I thought it was weird too, but the system you're working on was a replacement for an older system. Our requirements were derived from those. Let me think... Irving worked on that, but he's dead, god rest him. Penny is retired. Oh, you know, Humbert is still around. He didn't work on that, but he worked on some of the systems that came before that. He's upstairs and on the other side of the building."Eric went upstairs and to the other side of the building. The fourth floor had been last remodeled circa 1985, and the ugly industrial paint on the wall was made even uglier by the fact that someone had replaced most of the flourescent tubes with LEDs. Most. The mismatched color temperature started Eric down the path of a headache.Humbert was in an office similar to Elise's. On his desk was a plaque commemerating 40 years of service with the company. Eric asked about the limitation, and Humbert laughed."You're working on the latest version of a product that initially started on an old PDP-11 running MUMPS. I mean, the first versions, anyway. We ran to desktop computers as fast as we could. I wrote a version for DOS in... oh... '86? I knew none of the facilities we worked with had more than ten or fifteen racks of tubes, and I needed somehow to limit the size of the database so it all fit on a single 5 1/4" floppy disk. I picked thirty, because it seemed like a good round number. Honestly, I'm shocked that the limit still exists."So was Eric. There had been several ground-up-rewrites since 1986, before the one Eric maintained had been released thirteen years ago. Each one of them had chosen to maintain the same limitation, without ever considering why it existed. The rule had simply been copied, mindlessly, for 40 years."I'm kind of impressed," Eric said to Humbert, "in a horrified way.""Me too, kid, me too." [Advertisement] Keep all your packages and Docker containers in one place, scan for vulnerabilities, and control who can access different feeds. ProGet installs in minutes and has a powerful free version with a lot of great features that you can upgrade when ready.Learn more.
|
 |
by Remy Porter on (#752E2)
"Here, you're a programmer, take this over. It's business critical."That's what Felicity's boss told her when he pointed her to a network drive containing an Excel spreadsheet. The Excel spreadsheet contained a pile of macros. The person who wrote it had left, and nobody knew how to make it work, but the macros in question were absolutely business vital.Also, it's in French.We'll take this one in chunks. The indentation is as in the original.
|
 |
by Lyle Seaman on (#750PT)
It's time again for a reader special, and once again it's all The Beast In Black (there must be a story to that nick, no?)."MySQL is not better than your SQL," he pontificated, "especially whenit comes to the Workbench Migration Wizard"
|
 |
by Remy Porter on (#74ZV8)
Nona writes: "this is the beginning of a 2100 line function."That's bad. Nona didn't send us the entire JavaScript function, but sent us just the three early lines, which definitely raise concerns:
|
 |
by Remy Porter on (#74YXS)
Candice (previously) has another WTF to share for us.We're going to start by just looking at one fragment of a class defined in this C++ code: TLAflaList.Every type and variable has a three-letter-acronym buried in its name. The specific meaning of most of the acronyms are mostly lost to time, so "TLA" is as good as any other three random letters. No one knows what "fla" is.What drew Candice's attention was that there was a type called "list", which implies they're maybe not using the standard library and have reinvented a wheel. Another data point arguing in favor of that is that the class had a method called getNumElements, instead of something more conventional like size.Let's look at that function:
|
 |
by Remy Porter on (#74Y12)
Theresa works for a company that handles a fair bit of personally identifiable information that can be tied to health care data, so for them, security matters. They need to comply with security practices laid out by a variety of standards bodies and be able to demonstrate that compliance.There's a dirty secret about standards compliance, though. Most of these standards are trying to avoid being overly technically prescriptive. So frequently, they may have something like, "a process must exist for securely destroying storage devices before they are disposed of." Maybe it will include some examples of what you could do to meet this standard, but the important thing is that you have to have a process. This means that if you whip up a Word document called "Secure Data Destruction Process" and tell people they should follow it, you can check off that box on your compliance. Sometimes, you need to validate the process; sometimes you need to have other processes which ensure this process is being followed. What you need to do and to what complexity depends on the compliance structure you're beholden to. Some of them are surprisingly flexible, which is a polite way of saying "mostly meaningless".Theresa's company has a process for safely destroying hard drives. They even validated it, shortly after its introduction. They even have someone who checks that the process has been followed. The process is this: in the basement, someone set up a cheap drill press, and attached a wooden jig to it. You slap the hard drive in the jig, turn on the drill, and brrrrzzzzzz- poke a hole through the platters making the drive unreadable.There's just one problem with that process: the company recently switched to using SSDs. The SSDs are in a carrier which makes them share the same form factor as old-style spinning disk drives, but that's just a thin plastic shell. The actual electronics package where the data is stored is quite small. Small enough, and located in a position where the little jig attached to the drill guarantees that the drill won't even touch the SSD at all.For months now, whenever a drive got decommissioned, the IT drone responsible for punching a hole through it has just been drilling through plastic, and nothing else. An unknown quantity of hard drives have been sent out for recycling with PII and health data on them. But it's okay, because the process was followed.The compliance team at the company will update the process, probably after six months of meetings and planning and approvals from all of the stakeholders. Though it may take longer to glue together a new jig for the SSDs. [Advertisement] BuildMaster allows you to create a self-service release management platform that allows different teams to manage their applications. Explore how!
|
 |
by Remy Porter on (#74X5H)
Tim (previously) supports a relatively ancient C++ application. And that creates some interesting conundrums, as the way you wrote C++ in 2003 is not the way you would write it even a few years later. The standard matured quickly.Way back in 2003, it was still common to use C-style strings, instead of the C++ std::string type. It seems silly, but people had Strong OpinionsTM about using standard library types, and much of your C++ code was probably interacting with C libraries, so yeah, C-strings stuck around for a long time.For Tim's company, however, the migration away from C-strings was in 2007.So they wrote this:
|
 |
by Lyle Seaman on (#74VD5)
"My thoughts exactly" muttered Jason H."I was in a system that avoids check constraints andthe developers never seemed to agree to a T/F orY/N or 1/0 for indicator columns. All data in acolumn will use the same pattern but different columns inthe same table will use different patterns so I'm notsure why I was surprised when I came across theattached. Sort the data descending and you have the shorthandfor what I uttered." How are these all unique?
|
 |
by Remy Porter on (#74THB)
When looking at the source of a major news site, today's anonymous submitter sends us this very, very mild, but also very funny WTF:
|
 |
by Remy Porter on (#74ST3)
The father of the "billion dollar mistake" left us last month. His pointer is finally null. Speaking of null handling, Randy says he was "spelunking" through his codebase and found this pair of functions, which handles null.
|
 |
by Remy Porter on (#74RXZ)
Tim H inherited some code which has objects that have many, many properties properties on them. Which is bad. That clearly has no cohesion. But it's okay, there's a validator function which confirms that object is properly populated.The conditions and body of the conditionals have been removed, so we can see what the flow of the code looks like.
|
 |
by Remy Porter on (#74R7F)
Today's anonymous submission is one of the entries where I look at it and go, "Wait, that's totally wrong, that could have never worked." And then I realize, that's why it was submitted: it was absolutely broken code which got to production, somehow.
|
 |
by Lyle Seaman on (#74PNE)
An anonymous cable-puller wrote "Reading a long specification manual.The words "shall" and "shall not" have specific meaning,and throughout the document are in bold italic. Lookslike someone got a bit shall-ow with their search-and-replaceskills."
|
 |
by Remy Porter on (#74NTA)
I feel like we've gotten a few SQL case statement abuses recently, but a properly bad one continues to tickle me. Ken C sends us one that, well:
|
 |
by Remy Porter on (#74N3N)
You've already read the longer version. You need a quick phrase of corpo-speak to distract and confuse your rivals. Here's the generator for doing that: Generate Now, admittedly, this generator may use a grammar for generating phrases, but it's not an English grammar, and the result is that sometimes it has problems with verb agreement and other prosaic English rules. I say, lean into it. Let someone challenge your bad grammar, and then look down your nose at them, and say: "I'm blue-skying the infosphere across new domains, you wouldn't get it." [Advertisement] Keep the plebs out of prod. Restrict NuGet feed privileges with ProGet. Learn more.
|
 |
by Remy Porter on (#74MYS)
As we all know, there are two basic kinds of scientific studies. The first is a ground-breaking paper that changes the way we view the world, and forces us to confront our presuppositions and biases about how we think the world works, and change our perspective. The other tells us what we already know to be true, and makes us feel good. The second kind, of course, is what we'd call "good science".Or, if you want to skip past this straight to the generator at the bottom.For example, what if I told you that people who are impressed by hyperbolic corporate jargon are dumber than you or I? It's probably something you already believe is true, but wouldn't you like a scientist to tell you that it's true?Well, have I got good news for you. If you're tired of hearing about "growth-hacking paradigms" researchers at Cornell found that people who are impressed by semantically empty phrases are also bad at making decisions.The entire paper is available, if you like charts.There are a few key highlights worth reading, though. The paper spends a fair bit of time distinguishing between "jargon" and "bullshit". Jargon is domain specific language that is impenetrable to "out-group" individuals, while bullshit may be just as impenetrable, but also is "semantically empty and confusing".It also has some ideas about why we drift from useful jargon to bullshit. It starts, potentially, as a way to navigate socially difficult situations by blunting our speech: I can't say that I think you're terrible at your job, but I can say you need to actualize the domain more than you currently are. But also, it's largely attempts to fluff ourselves up, whether it's trying to contribute to a meeting when we haven't an idea what we're talking about, or trying to just sound impressive or noble in public messaging. It seems that the backbone of bullshit is the people who didn't do the reading for Literature class but insist on holding forth during the classroom discussion, confident they can bullshit their way through.Of course, bullshit doesn't thrive unless you have people willing to fall for it. And when it comes to that, it's worth quoting the paper directly:
|
 |
by Remy Porter on (#74M3D)
Sandra from InitAg (previously) works with Bjorn, and Bjorn has some ideas about how database schemas should be organized.First, users should never see an auto-incrementing ID. That means you need to use UUIDs. But UUIDs are large and expensive, so they should never be your primary key, use an auto-incrementing ID for that.This is not, in and of itself, a radical or ridiculous statement. I've worked on many a database that followed similar rules. I've also seen "just use a UUID all the time" become increasingly common, especially on distributed databases, where incrementing counters is expensive.One can have opinions and disagreements about how we handle IDs in a database, but I wouldn't call anything a WTF there.No, the WTF is how Bjorn would design his cross-reference tables. You know, the tables which exist to permit many-to-many relationships between two other tables? Tables that should just be tableA.id and tableB.id?
|