 |
by Alex Papadimoulis on (#2VYBA)
|
 The Daily WTF
The Daily WTF
| Link | http://thedailywtf.com/ |
| Feed | http://syndication.thedailywtf.com/TheDailyWtf |
| Updated | 2026-06-09 14:30 |
 |
by Mark Bowytz on (#2VB3Q)
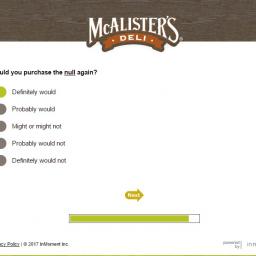
"Truly the best null I've ever had. Definitely would purchase again," wrote Andrew R.
|
by Mark Bowytz on (#2VYBB)
"Truly the best null I've ever had. Definitely would purchase again," wrote Andrew R.
 |
by Remy Porter on (#2V81J)
In addition to our “bread and butter†of bad code, bad bosses, worse co-workers and awful decision-making, we always love the chance to turn out occassional special events. This time around, our sponsors at Hired gave us the opportunity to build and film a sketch.I’m super-excited for this one. It’s a bit more ambitious than some of our previous projects, and pulled together some of the best talent in the Pittsburgh comedy community to make it happen. Everyone who worked on it- on set or off- did an excellent job, and I couldn't be happier with the results.Once again, special thanks to Hired, who not only helped us produce this sketch, but also helps keep us keep the site running. With Hired, instead of applying for jobs, your prospective employer will apply to interview you. You get placed in control of your job search, and Hired provides a “talent advocate†who can provide unbiased career advice and make sure you put your best foot forward. Sign up now, and find the best opportunities for your future with Hired. And now, our feature presentation: The AgreementBrought to you by:
|
 |
by Remy Porter on (#2VYBC)
In addition to our “bread and butter†of bad code, bad bosses, worse co-workers and awful decision-making, we always love the chance to turn out occassional special events. This time around, our sponsors at Hired gave us the opportunity to build and film a sketch.I’m super-excited for this one. It’s a bit more ambitious than some of our previous projects, and pulled together some of the best talent in the Pittsburgh comedy community to make it happen. Everyone who worked on it- on set or off- did an excellent job, and I couldn't be happier with the results.Once again, special thanks to Hired, who not only helped us produce this sketch, but also helps keep us keep the site running. With Hired, instead of applying for jobs, your prospective employer will apply to interview you. You get placed in control of your job search, and Hired provides a “talent advocate†who can provide unbiased career advice and make sure you put your best foot forward. Sign up now, and find the best opportunities for your future with Hired. And now, our feature presentation: The AgreementBrought to you by:
|
 |
by Remy Porter on (#2V4X6)
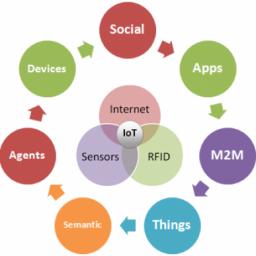
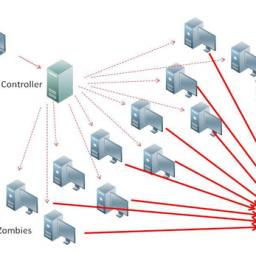
Folks, we’ve got to talk about some of the headlines about the Internet of “Thingsâ€. If you’ve been paying even no attention to that space, you know that pretty much everything getting released is some combination of several WTFs, whether in conception, implementation, and let’s not forget security.I get it. It’s a gold-rush business. We’ve got computers that are so small, so cheap, and so power-efficient, that we can slap the equivalent of a 1980s super-computer in a toilet seat. There's the potential to create products that make our lives better, that make the world better, and could carry us into a glowing future. It just sometimes feels like that's not what anybody's actually trying to make, though. Without even checking, I’m sure you can buy a WiFi enabled fidget spinner that posts the data to a smartphone app where you can send “fidges†to your friends, bragging about your RPMs.We need this news-roundup, because when Alexa locks you out of your house because you didn’t pay for Amazon Prime this month, we can at least say “I told you soâ€. You think I’m joking, but Burger King wants in on that action, with its commercial that tries to trick your Google Assistant into searching for burgers. That’s also not the first time that a commercial has trigged voice commands, and I can guarantee that it isn’t going to be the last.Now, maybe this is sour grapes. I bought a Nest thermostat before it was cool, and now three hardware generations on, I’m not getting software updates, and there are rumors about the backend being turned off someday. Maybe Nest needs a model more like “Hive Hubâ€. Hive is a startup with £500M invested, making it one of the only “smart home†companies with an actual business model. Of course, that business model is that you’ll pay $39.99 per month to turn your lights on and off.At least you know that some of that money goes to keeping your smart-home secure. I’m kidding, of course- nobody spends any effort on making these devices secure. There are many, many high profile examples of IoT hacks. You hook your toaster up to the WiFi and suddenly it’s part of a botnet swarm mining BitCoins. One recent, high-profile example is the ZigBee Protocol, which powers many smart-home systems. It’s a complete security disaster, and opens up a new line of assault- instead of tricking a target to plug a thumb drive into their network, you can now put your payload in a light bulb.Smart-homes aside, IoT in general is breeding ground for botnets. Sure, your uncle Jack will blindly click through every popup and put his computer password in anything that looks like a password box, but at least you can have some confidence that his Windows/Mac/Linux desktop has some rudimentary protections bundled with the OS. IoT vendors apparently don’t care.Let’s take a break, and take a peek at a fun story about resetting a computerized lock. Sure, they could have just replaced the lock, but look at all the creative hackery they had to do to get around it.With that out of the way, let’s talk about tea. Ever since the Keurig coffee maker went big, everyone’s been trying to be “the Keurig for waffles†or “the Keurig for bacon†or “the Keurig for juiceâ€- the latter giving us the disaster that is the Juicero. Mash this up with the Internet of Things, and you get this WiFi enabled tea-maker, which can download recipes for brewing tea off the Internet. And don’t worry, it’ll always use the correct recipe because each pod is loaded with an RFID that not only identifies which recipe to use, but ensures that you’re not using any unathorized tea.In addition to the “Keurig, but for $X,†there’s also the ever popular “the FitBit, but for $X.†Here’s the FitBit for desks. It allows your desk to nag you about getting up, moving around, and it’ll upload your activity to the Internet while it’s at it. I’m sure we’re all really excited for when our “activity†gets logged for future review.Speaking of FitBits, Qualcomm just filed some patents for putting that in your workout shoes. This is actually not a totally terrible idea- I mean, by standards of that tea pot, anyway. I share it here because they’re calling it “The Internet of Shoes†which is a funny way of saying, “our marketing team just gave upâ€.Finally, since we’re talking about Internet connected gadgets that serve no real purpose, Google Glass got its first software update in three years. Apparently Google hasn’t sent the Glass to a farm upstate, where it can live with Google Reader, Google Wave, Google Hangouts, and all the other projects Google got bored of. [Advertisement] Application Release Automation – build complex release pipelines all managed from one central dashboard, accessibility for the whole team. Download and learn more today!
|
 |
by Charles Robinson on (#2V1VM)
Joe K was a developer at a company that provided a SaaS Natural Language Processing system. As Chief Engineer of the Data Science Team (a term that make him feel like some sort of mad professor), his duties included coding the Data Science Service. It provided the back-end for handling the complex, heavy-lifting type of processing that had to happen in real-time. Since it was very CPU-intensive, Joe spent a lot of time trying to battle latency. But that was the least of his problems.The rest of the codebase was a cobbled-together mess that had been coded by the NLP researchers- scientists with no background in programming or computer science. Their mantra was “If it gets us the results we need, who cares how it looks behind the scenes?†This meant Joe’s well-designed data service somehow had to interface with applications made from a pile of ugly hacks. It was difficult at times, but he managed to get the job done while also keeping CPU usage to a minimum.One day Joe was working away when Burt, the company CEO, burst in to their humble basement computer lab in an obvious tizzy. Burt rarely visited the “egghead dungeonâ€, as he called it, so something had to be amiss. “JOE!†he cried out. “The production data science service is completely down! Every customer we have gave me an angry call within the last ten minutes!â€Considering this was an early-stage startup with only five customers, Burt’s assertion was probably true, if misleading. “Wow, ok Burt. Let me get right on that!†Joe offered, feeling flustered. He took a look at the error logging service and there was nothing to be found. He then attempted to SSH to each of the production servers, with success. He decided to check performance on the servers and an entire string of red flags shot straight up the proverbial flag pole. Every production server was at 100% CPU usage.“I have an effect for you, Burt, but not a cause. I’ll have to dig deeper but it almost seems like… a Denial of Service attack?†Joe offered, not believing that would actually be the case. With only five whitelisted customers able to connect, all of them using the NLP system to its fullest shouldn’t come even close to causing this.While looking further at the server logs, Joe got an instant message from Xander, the software engineer who worked on the dashboards, “Hey Joe, I noticed prod was down… could it be related to something I’m doing?â€â€œUmmm… maybe? What is it you are doing exactly?†Joe replied, with a new sense of concern. Xander’s dashboard shouldn’t have any interaction with the DSS, so it seemed like an odd question. Requests to the NLP site would initially come to a front-end server, and if there was some advanced analysis that needed to happen, that server would RPC to the DSS. After the response was computed, the front-end server would log the request and response to the Xander’s dashboard system so it could monitor usage stats.“Well, the dashboard is out of sync,†Xander explained. There had been a bug causing events to not make it to the dashboard system for the past month. They would need to be added to make the dashboard accurate. This could have been a simple change to the dashboard’s database, but instead Xander decided to replay all of the actual HTTP requests to the front end. Many of those requests triggered processing on the DSS- processing which had already been done. And since it was taking a long time, Xander had batched up the resent requests and was running them from three different machines, thus providing a remarkably good simulation of a DDoS.“STOP YOUR PROCESS IMMEDIATELY AND DO THIS THE RIGHT WAY!†Joe shot back, all caps intended.“Ok, ok, sorry. I’ll get this cleaned up,†Xander assured Joe. Within 15 minutes, the server CPU usage returned to normal levels and everything was great again. Joe was able to get Burt off his back and return to his normal duties.A few minutes later, Joe’s IM dinged again with a message from Xander. "Hey Joe, sorry about that, LOL. But are we 100% sure that was the problem? Should I do it again just to be sure?If there was a way for Joe to use instant messaging to send a virtual strangulation to Xander, he would have done it. But a “HELL NO!!!†would have to suffice.[Advertisement] Release!is a light card game about software and the people who make it. Play with 2-5 people, or up to 10 with two copies - only $9.95 shipped!
|
 |
by Ellis Morning on (#2TYQM)
Today, submitter Adam shows us how thoughtless language assumptions made by programmers are also hilarious language assumptions:
|
by Mark Bowytz on (#2TQRV)
"Outlook can't open an attachment because it claims that it was made in Outlook, which Outlook doesn't think is installed...or something," writes Gavin.
 |
by Ellis Morning on (#2TMN8)
Shawn W. was a newbie support tech at a small company. Just as he was beginning to familiarize himself with its operational quirks, he got a call from Jim: The Big Boss.Dread seized Shawn. Aside from a handshake on Interview Day, the only "interaction" he'd had with Jim thus far was overhearing him tear into a different support rep about having to deal with "complicated computer crap" like changing passwords. No doubt, this call was bound to be a clinic in saintly patience."Tech Support," Shawn greeted. "How may—?""I'm out of space and I need more!" Jim barked over the line."Oh." Shawn mentally geared up for a memory or hard drive problem. "Did you get a warning or error mes—?""Just get up here and bring some more space with you!" Jim hung up."Oh, boy," Shawn muttered to himself.Deciding that he was better off diagnosing the problem firsthand, Shawn trudged upstairs to Jim's office. To his pleasant surprise, he found it empty. He sank into the cushy executive-level chair. Jim hadn't been away long enough for any screensavers or lock screens to pop up, so Shawn had free rein to examine the machine.There wasn't much to find. The only program running was a web browser, with a couple of tabs open to ESPN.com and an investment portfolio. The hardware itself was fairly new. CPU, memory, hard drive all looked fine."See, I'm out of space. Did you bring me more?"Shawn glanced up to find Jim barreling toward him, steaming mug of coffee in hand. He braced himself as though facing down an oncoming freight train. "I'm not sure I see the problem yet. Can you show me what you were doing when you noticed you needed more space?"Jim elbowed his way over to the mouse, closed the browser, then pointed to the monitor. "There! Can't you see I'm out of space?"Indeed, Jim's desktop was full. So many shortcuts, documents, widgets, and other icons crowded the screen that the tropical desktop background was barely recognizable as such.While staring at what resembled the aftermath of a Category 5 hurricane, Shawn debated his response. "OK, I see what you mean. Let's see if we can—""Can't you just get me more screen?" Jim pressed.More screen? "You mean another monitor?" Shawn asked. "Well, yes, I could add a second monitor if you want one, but we could also organize your desktop a little and—""Good, get me one of those! Don't touch my icons!" Jim shooed Shawn away like so much lint. "Get out of my chair so I can get back to work."A short while later, Shawn hooked up a second monitor to Jim's computer. This prompted a huge and unexpected grin from the boss. "I like you, you get things done. Those other guys would've taken a week to get me more space!"Shawn nodded while stifling a snort. "Let me know if you need anything else."Once Jim had left for the day, Shawn swung past the boss' office out of morbid curiosity. Jim had already scattered a few dozen shortcuts across his new real estate. Another lovely vacation destination was about to endure a serious littering problem.[Advertisement] Manage IT infrastructure as code across all environments with Puppet. Puppet Enterprise now offers more control and insight, with role-based access control, activity logging and all-new Puppet Apps. Start your free trial today!
|
 |
by Remy Porter on (#2THGQ)
The innermost circle of Hell, as we all know, is trying to resolve printer driver issues for all eternity. Ben doesn’t work with the printers that we mere mortals deal with on a regular basis, though. He runs a printing press, three stories of spinning steel and plates and ink and rolls of paper that could crush a man.Like most things, the press runs Linux- a highly customized, modified version of Linux. It’s a system that needs to be carefully configured, as “disaster recovery†has a slightly different meaning on this kind of heavy equipment. The documentation, while thorough and mostly clear, was obviously prepared by someone who speaks English as a second language. Thus, Ben wanted to check the shell scripts to better understand what they did.The first thing he caught was that each script started with variable declarations like this:
|
 |
by Jane Bailey on (#2TE9G)
Contracting can be really hit or miss. Sometimes, you're given a desk and equipment and treated just like an employee, except better paid and exempt from team-building exercises. Sometimes, however, you're isolated in your home office, never speaking to anyone, working on tedious, boring crap they can't convince their normal staff to do.Eric was contracted to perform basic website updating tasks for a government agency. Most of the work consisted of receiving documents, uploading them to the server, and adding them to a page. There were 4 document categories, each one organized by year. Dull as dishwater, but easy.The site was hosted by a third party in a shared hosting environment. It ran on a CMS produced by another party. WTFCMS was used in many high-profile sites, so the agency figured it had to be good. Eric was given login credentials and—in the way of techies given boring tasks everywhere—immediately began automating the task at hand.Step 1 of this automation was to get a list of articles with their IDs. Eric was pleased to discover that the browser-based interface for the CMS used a JSON request to get the list of pages. With the help of good old jq, he soon had that running in a BASH shell script. To get the list of children for an article, he passed the article's ID to the getChildren endpoint.Usually, in a heirarchy like this, there's some magic number that means "root element." Eric tried sending a series of likely candidates, like 0, -1, MAX_INT, and MIN_INT. It turned out to be -1 ... but he also got a valid list when he passed in 0.Curious, he thought to himself. This appears to be a list of articles ... and hey, here's the ones I got for this site. These others ...? No way.Sure enough, passing in a parent ID of 0 had gotten Eric some sort of super-root: every article across every site in the entire CMS system. Vulnerability number 1.Step 2 was to take the ID list and get the article data so he could associate the new file with it. This wasn't nearly as simple. There was no good way to get the text of the article from the JSON interface; the CMS populated the articles server-side.Eric was in too deep to stop now, though. He wrote a scraper for the edit page, using an XML parser to handle the HTML form that held the article text. Once he had the text, he compared it by hand to the POST request sent from his Firefox instance to ensure he had the right data.And he did ... mostly. Turns out, the form was manipulated by on-page Javascript before being submitted: fields were disabled or enabled, date/time formats were tweaked, and the like. Eric threw together some more scripting to get the job done, but now he wasn't sure if he would hit an edge case or somehow break the database if he ran it. Still, he soldiered on.Step 3 was to upload the files so they could be linked to the article. With Firebug open, Eric went about adding an upload.Now, WTFCMS seemed to offer the usual flow: enter a name, select a file, and click Upload to both upload the file and save it as the given name. When he got to step 2, however, the file was uploaded immediately—but he still had to click the Upload button to "save" it.What happens if I click Cancel? Eric wondered. No, never mind, I don't want to know. What does the POST look like?It was a mess of garbage. Eric was able to find the file he uploaded, and the name he'd given it ... and also a bunch of server-side information the user shouldn't be privvy to, let alone be able to tamper with. Things like, say, the directory on the server where the file should be saved. Vulnerability number 2.The response to the POST contained, unexpectedly, HTML. That HTML contained an iframe. The iframe contained an iframe. iframe contained iframe; iframe contained a form. In that form were two fields: a submit button, reading "Upload", and a hidden form field containing the path of the uploaded file. In theory, he could change that to read anything on the server. Now he had both read and write access to any arbitrary destination in the CMS, maybe even on the server itself. Vulnerability number 3.It was at this point that Eric gave up on his script altogether. This is the kind of task that Selenium IDE is perfect for. He just kept his head down, hoped that the server had some kind of validation to prevent curious techies like himself from actually exploiting any of these potential vulnerabilities, and served out the rest of his contract.[Advertisement] Release!is a light card game about software and the people who make it. Play with 2-5 people, or up to 10 with two copies - only $9.95 shipped!
|
 |
by Remy Porter on (#2TB96)
For a brief period of time, say, about 3–4 years ago, if you wanted to sound really smart, you’d bring up “functional programmingâ€. Name-dropping LISP or even better, Haskell during an interview marked you as a cut above the hoi polloi. Even I, surly and too smart for this, fell into the trap of calling JavaScript “LISP with curly bracesâ€, just because it had closures.Still, functional programming features have percolated through other languages because they work. They’re another tool for the job, and like any tool, when used by the inexpert, someone might lose a finger. Or perhaps someone should lose a finger, if only as a warning to others.For example, what if you wanted to execute a loop 100 times in JavaScript? You could use a crummy old for loop, but that’s not functional. The functional solution comes from an anonymous submitter:
|
 |
by Mark Bowytz on (#2T4BE)
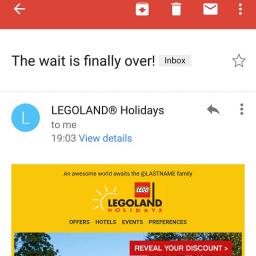
"I asked my son, @Firstname, and he is indeed rather @Emotion about going to @ThemePark!" wrote Chris @LASTNAME.
|
 |
by Mark Bowytz on (#2T1CR)
|
 |
by Alex Papadimoulis on (#2SXSF)
|
 |
by Alex Papadimoulis on (#2SSR0)
|
 |
by Alex Papadimoulis on (#2SNS4)
|
 |
by Mark Bowytz on (#2SCBS)
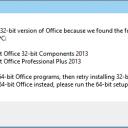
"I know software can't always be perfect, but things like this make me want to shut down my PC and say that's enough computering for the day," writes Timothy W.
|
 |
by Remy Porter on (#2S8NW)
“Staff augmentation,†was a fancy way of saying, “hey, contractors get more per hour, but we don’t have to provide benefits so they are cheaper,†but Stuart T was happy to get more per hour, and even happier to know that he’d be on to his next gig within a few months. That was how he ended up working for a national chain of gas-station/convenience stores. His job was to build a “new mobile experience for customer loyalty†(aka, wrapping their website up as an app that can also interact with QR codes).At least, that’s what he was working on before Miranda stormed into his cube. “Stuart, we need your help. ProdTrack is down, and I can’t fix it, because I’ve got to be at a mandatory meeting in ten minutes.â€ProdTrack was their inventory system that powered their point-of-sale terminals. For it to be down company wide was a big problem, and essentially rendered most of their stores inoperable. “Geeze, what mandatory meeting is more important than that?â€â€œThe annual team-building exercise,†Miranda said, using a string of profanity for punctuation. “They’ve got a ‘no excuses’ policy, so I have to go, ‘or else’, but we also need to get this fixed.â€Miranda knew exactly what was wrong. ProdTrack could only support 14 product categories. But one store- store number 924- had decided that they needed 15. So they added a 15th category to the database, threw a few products into the category, and crossed their fingers. Now, all the stores were crashing.“You’ll need to look at the StoreSQLUpdates and the StoreSQLUpdateStatements tables,†Miranda said. “And probably dig into the ProductDataPump.exe app. Just do a quick fix- we’re releasing an update supports any number of categories in three weeks or so, we just need to hold this together till then.â€With that starting point, Stuart started digging in. First, he puzzled over the tables Miranda had mentioned. StoreSQLUpdates looked like this:IDSTATEMENTSTATEMENT_ORDER145938DELETE FROM SupplierInfo90148939INSERT INTO ProductInfo VALUES(12348, 3, 6)112Was this an audit tables? What was StoreSQLUpdateStatements then?IDSTATEMENT168597INSERT INTO StoreSQLUpdates(statement, statement_order) VALUES (‘DELETE FROM SupplierInfo’, 90)168598INSERT INTO StoreSQLUpdates(statement, statement_order) VALUES (‘INSERT INTO ProductInfo VALUES(12348, 3, 6)’, 112)Stuart stared at his screen, and started asking questions. Not questions about what he was looking at, but questions about the life choices that had brought him to this point, questions about whether it was really that bad an idea to start drinking at work, and questions about the true nature of madness- if the world was mad, and he was the only sane person left, didn’t that make him the most insane person of all?He hoped the mandatory team building exercise was the worst experience of Miranda’s life, as he sent her a quick, “WTF?†email message. She obviously still had her cellphone handy, as she replied minutes later:
|
 |
by Remy Porter on (#2S4WB)
Asynchronous programming is hard, and there’s never been a perfect way to solve that problem. One of the most widely used solutions is the “promise†or “futureâ€. We wrap the asynchronous process up in a, well, promise of a future result. “Someday, there will be data here, I hope.†The real beauty of promises comes from their composability- “getData promises to fetch some records, and then the calling method can promise to display them.â€Of course, it’s still asynchronous, and when an application has multiple asynchronous processes happening at the same time, “weird behavior†can happen, thanks to timing issues. Keith W encountered one of those timing related Heisenbugs, and became immediately suspicious about how it was getting invoked:
|
by snoofle on (#2S0TP)
When designing a new feature of an application, among other things, you always want to decide how it will be used. Is it single threaded or will it need to happen in parallel. Will only one user do it at a time, or does it need to support asynchronous access. Will every user want to do it in the same way, or will they each want something just a little different.Charlie C. worked for a modestly sized financial startup that had gained some traction. The company had grown to about 100 people. They had garnered about 300 customers, and they were building software that would solve a problem that was causing regulators all manner of headaches.The system essentially provided the ability for customers to swap bond insurance contracts. These swaps could be between any two, three or four parties, depending upon the type of transaction. One day, one of the customers asked the CEO if they could implement an approval workflow. Specifically, before letting some low level trader execute a swap, it would be routed to a group with approval authority. If approved, the transaction would be routed to the other party. If not, it would be rejected back to the initiator.The CEO asked the development manager who came to Charlie and told him to just hard code some flags in the main transaction record, and check for them as special cases at every relevant place in the code. Charlie knew that if one customer wanted it, that most (if not all) of them would want it. Accordingly, he explained as much and said he would make it table driven."Won't that take longer to build?" the boss inquired."Of course it will take longer, but it's a whole lot more supportable than special-casing the code all over, and corrupting the main transaction record," Charlie replied. With 300 customers and transactions involving 2, 3 or 4 parties, there were almost 8 billion permutations; even a tiny fraction of customers requesting special handling would make it absolutely unsupportable. "Think of it like… insurance."The manager insisted on the hard coding, but Charlie ignored him, knowing all too well the consequences of listening to his boss.A few months later, the work was done. On the very last day of work, as Charlie was doing some final cleanup, his boss walked over with the CEO in tow. They were both in a bit of a panic. "Another customer has asked for special workflow processing, but in a slightly different way. How much time will it take to add the additional workflow logic?"Charlie looked at his boss, laughed, and said "About thirty minutes.""But it took months this time!""And this is why I don't listen to you." Charlie went on to explain that it would take about a half hour to create the relevant groups, users and flags to simulate the new workflow, and that he would try to start the servers, queue managers and 16 copies of their application (one for each user in the scenario) on his PC to demonstrate that it would perform the required routing.At the appointed time, both CEO and development manager returned and watched as Charlie made his machine groan through the motions to perform the desired flow processing. While it was busy thrashing, he used the opportunity to point out that they had no demo environment, that the developer workstations were simply not powerful enough to perform these sorts of demos, and he apologized for taking so much of their time. As the CEO listened to the hard disk grinding away, he agreed and offered to let them buy more powerful developer workstations.After about an hour of going through all the different scenarios, the CEO was pleased, thanked Charlie for his time and told him to put in an order for the workstations the next day. Then they walked away.Later that day, the development manager was transferred to manage another team and someone else was put in charge of Charlie's project. Shortly thereafter, Charlie grabbed the other developers and put together specs for their dream machines, which were ordered the next day.Over the next year, configurations for more than a thousand different special case workflows were added, and not a single byte of code had to change.[Advertisement] Manage IT infrastructure as code across all environments with Puppet. Puppet Enterprise now offers more control and insight, with role-based access control, activity logging and all-new Puppet Apps. Start your free trial today!
 |
by Remy Porter on (#2RWV6)
If you’re not already aware, the Daily WTF is open source. We went the route of building our own CMS mostly because our application needs are pretty light. We don’t need themes, we don’t need WYSIWYG editors, we don’t need asset uploads. Also, with home-grown code, we know what’s in it, what it does, and any problems in the code are our own.Which brings us to WordPress, land of the themes. There’s a cottage industry around building WordPress themes, and it’s a busy enough space that there are specialists in developing themes for specific industries. Alessandro ended up doing some work in the real estate business, tweaking a WP theme to change the way certain images would get displayed in a slide show.
|
 |
by Mark Bowytz on (#2RKMP)
John A. wrote, "Wait, so 'Cancel' is 'Continue' and 'OK' is really 'Cancel'!?"
|
 |
by Remy Porter on (#2RFMN)
Twelve years ago, a company decided they needed a website. They didn’t have any web developers, and they didn’t want to hire any, so they threw a PHP manual at the new hire who happened to “be good with computersâ€, and called it a day.Ms. “Good With Computers†actually learned something from the experience, and moved on to a lucrative career in web development. Unfortunately, she left behind the code she learned by doing, and now Bert has been brought in to clean up the code.Take this block, which translates an airport code into a location name…
|
 |
by Erik Gern on (#2RBCE)
Fresh out of college and out of money, Johan K. started work at Midgard Manufacturing as a junior developer. His supervisor Ragna made it clear: he would only be responsible for coding error handlers.“Our plant equipment is several decades old,†she said, “and we have to rely on the manufacturer-provided documentation for adequate coverage. To be honest, none of the senior developers want to bother. So instead of bothering one of them, you’ll be doing it.â€Johan didn’t have a problem with this. He knew he’d have to earn his chops at Midgard. But after he was given the stack of manuals that towered over his monitor, he wondered just how long it would take.Pride Goeth Before a FallOne month later, he had made it through a hundred pages of the first manual. Ragna checked in periodically, more interested in how complete his code was than how quickly he was getting through his list of error conditions.The manual he was working on was for a steel press. Vintage 1985, the steel press’s firmware - using Microsoft Xenix - relied on the flakiest of communication protocols: passing information via temp file. Every night around 2AM, the press would go down for maintenance. A shell script, written by Johan, would read data from the temp file the steel press had created, enter it into a SQL database, then delete the file from disk.Half the lines of code in Johan’s script were if/then blocks, one for each condition listed in the manual.
|
 |
by Remy Porter on (#2R77W)
Interviewing developers always poses a challenge. You can’t rate their skills at writing code without seeing them write code, and most of the code they’ve written probably belongs to someone else. Writing anything non-trivial takes time, which both the candidate and the interviewer may not be willing to spend. Even then, it’s not always representative. And let’s not even talk about whiteboard programming.Douglas’s company makes a compromise- they’ll give a time-boxed programming challenge. A developer is given two hours, access to the Internet, and a moderately complex problem. A smart developer might make some mistakes on the trickier parts of the problems, which is great, because it doesn’t fail them- it shows how they think. One candidate, Steve, never quite got that far.At one point in the process, the code needs to determine if two dates are within 90 days of each other. Even in Java, this is a trivial task, worthy of one line of code. Possibly two, if you want to be super clear:
|
 |
by Alex Papadimoulis on (#2R3SD)
|
 |
by Mark Bowytz on (#2QTF0)
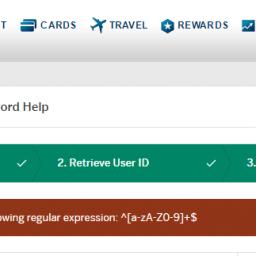
"Apparently, if AMEX's site knows that you're a developer, it will present a REGEX challenge before allowing you to reset your password," Jim wrote.
|
by Remy Porter on (#2QPJT)
Tim joined a company that provided a SaaS solution for tracking attendance and grades in schools. The job was mostly minor updates to a ColdFusion application, although there was an active project to replace it with something more modern. Tim felt like half of his hiring was based on him knowing when to throw out buzzwords like SPA or REST or Reactive Programming.“It’s not the first time,†Karmen explained. She’d been with the company for some time. “When I joined, they had just upgraded to ColdFusion from a VBA hack on Microsoft Access. Crazy days, back then, when the whole ‘selling service, not software’ thing was new. Sometimes, I think I was hired because I knew the right buzzwords.â€Ostensibly, Karmen and Tim were meant to be focused on the new version of the application, but the ColdFusion version was so old and so poorly maintained that they spent 75% of their time in firefighting mode. The rest of the team had neatly adapted to the culture of “just put out the fire, and don’t worry about code quality, there’ll be a new fire tomorrowâ€, which of course only created more fires to put out.One day, near the end of the month, the webmaster inbox had an alert message from their webhost.
 |
by Jane Bailey on (#2QJKB)
Recently, at my dayjob, I had a burning need to understand how scheduled tasks work. You see, we've recently switched from Adobe Coldfusion to Lucee, and I was shaky on how Adobe did things before, so I wanted a deeper understanding of how the code I was working on would be executed. For the uninitiated, Lucee is an open-source reimplementation of Cold Fusion. And that's not the WTF.It's open source, I thought to myself. I'll just take a look at the code.I had one problem. Then I looked at the code. Now I have two problems ... and a headache:
|
 |
by Remy Porter on (#2QE8D)
Rachel started working as a web developer for the local bus company. The job made her feel young, since the buses, the IT infrastructure, and most of their back-office code was older than she was. The bus fare-boxes were cash only, and while you could buy a monthly pass, it was just a little cardboard slip that you showed the driver. Their accounting system ran on a mainframe, their garage management software was a 16-bit DOS application. Email ran on an Exchange 5.5 server.In charge of all of the computing systems, from the web to DOS, was Virgil, the IT director. Virgil had been hired back when the accounting mainframe was installed, and had nestled into his IT director position like a tick. The bus company, like many such companies in the US, was ostensibly a private company, but chartered and subsidized by the city. This created a system which had all the worst parts of private-sector and public-sector employment merged together, and Virgil was the master of that system.Rachel getting hired on was one of his rare “lossesâ€, and he wasn’t shy about telling her so.“I’ve been doing the web page for years,†Virgil said. “It has a hit counter, so you can see how many hits it actually gets- maybe 1 or 2 a week. But management says we need to have someone dedicated to the website.†He grumbled. “Your salary is coming out of my budget, you know.â€That website was a FrontPage 2000 site, and the hit-counter was broken in any browser that didn’t have ActiveX enabled. Rachel easily proved that there was far more traffic than claimed, not that there was a lot. And why should there be? You couldn’t buy a monthly pass online, so the only feature was the ability to download PDFs of the hand-schedules.With no support, Rachel did her best to push things forward. She redesigned the site to be responsive. She convinced the guy who maintained their bus routes (in a pile of Excel spreadsheets) to give her regular exports of the data, so she could put the schedules online in a usable fashion. Virgil constantly grumbled about wasting money on a website nobody used, but as she made improvements, more people started using it.Then it was election season. The incumbent mayor had been complaining about the poor service the bus company was offering, the lack of routes, the costs, the schedules. His answer was, “cut their fundingâ€. Management started talking about belt-tightening, Virgil started dropping hints that Rachel was on the chopping block, and she took the hint and started getting resumes out.A miracle occurred. The incumbent mayor’s campaign went off the rails. He got caught siphoning money from the city to pay for private trips. A few local cops mentioned that they’d been called in to cover-up the mayor’s frequent DUIs. His re-election campaign’s finances show strange discrepancies, and money had come in that couldn’t be tied back to a legitimate contribution. He tried to get a newly built stadium named after himself, which wasn’t illegal, but was in poor taste and was the final straw. He dropped out of the election, paving the way for “Mayor Fred†to take over. Mayor Fred was a cool Mayor. He wanted to put in bike lanes. He wanted to be called “Mayor Fredâ€. He wanted to make it easier for food trucks to operate in the city. And while he shared his predecessor’s complaints about the poor service from the bus company, he had a different solution, which he revealed while taking a tour of the bus company’s offices.“I’m working right now to secure federal grants, private sector funding, to fund a modernization project,†Mayor Fred said, grinning from behind a lectern. “Did you know we’re paying more to keep our old buses on the road for five years than it would cost to buy new buses?†And thus, Mayor Fred made promises. Promises about new buses, promises about top-flight consultants helping them plan better routes, promises about online functionality.Promises that made Virgil grumble and whine. Promises that the mayor… actually kept. New buses started to hit the streets. They had GPS and a radio communication system that gave them up-to-the-second location reporting. Rachel got put in charge of putting that data on the web, with a public API, and tying it to their schedules. A group of consultants swung through to help, and when the dust settled, Rachel’s title was suddenly “senior web developer†and she was in charge of a team of 6 people, integrating new functionality to the website.Virgil made his opinion on this subject clear to her: “You are eating into my budget!â€â€œIsn’t your budget way larger?†Rachel asked.“Yes, but there’s so much more to spend it on! We’re a bus company, we should be focused on getting people moving, not giving them pretty websites with maps that tell them where the buses are! And now there’s that new FlashCard project!â€FlashCard was a big project that didn’t involve Rachel very much. Instead of cash fares and cardboard passes, they were going to get an RFID system. You could fill your card at one of the many kiosks around the city, or even online. “Online†of course, put it in Rachel’s domain, but it was mostly a packaged product. Virgil, of all people, had taken over the install and configuration, Rachel just customized the stylesheet so that it looked vaguely like their main site.Rachel wasn’t only an employee of the bus company, she was also a customer. She was one of the first in line to get a FlashCard. For a few weeks, it was the height of convenience. The stop she usually needed had a kiosk, she just waved her card at the farebox and paid. And then, one day, when her card was mostly empty and she wasn’t anywhere near a kiosk, she decided to try filling her card online.
|
 |
by Ellis Morning on (#2QADJ)
Every day in IT, each one of us walks the fine line between "brilliant" and "appalling." We come across things that make our jaws drop, and we're not sure whether we're amazed or horrified or both. Here's a PHP sample that Brett P. was lucky—or unlucky—enough to discover:
|
 |
by Mark Bowytz on (#2Q13G)
"Maybe it it compiled...maybe it didn't. I guess that I have to find out myself from here on out," wrote, Y. Diomidov.
|
by TJ Mott on (#2PX4J)
Ron used to work for a company which built “smell-o-visionsâ€. These were customized systems running small form factor Windows PCs that operated smell pumps and fans using USB relays timed to a video to give a so-called “4D Experience.†Their product was gimmicky, and thus absolutely loved by marketing groups.One such marketing group, whose client was a branch of the military, worked with them to create a gimmick to help with recruiting. A smell-o-vision was installed on a trailer and towed around the country, used to convince teenagers to join the service by making them smell fresh-squeezed orange juice while watching a seizure-inducing video with guns. The trailer was staffed by grunts, and these guys cycled through so frequently that they received little or no training on the system.“Hey Ron,†Sam, his boss, told him one day. “The recruiter is having a ton of trouble with their system and I need you to go on-site and take a look.â€Going on-site was the only option. The recruiter’s system was not on the Internet so remote diagnosis was impossible. And so he soon found himself cooking in the hot desert sun on a base in the Southwest, looking at a small LCD screen on a 1U pull-out tray accessible through an access panel in the trailer.“This is what it always does,†said the grunt assigned to work with him. “It always says it’s corrupted and the 4D stuff doesn’t work. Rebooting doesn’t fix it.â€Ron looked at the screen as the outdated Windows XP booted up and watched it flash an error stating “Windows was not properly shut down†before beginning a long filesystem scan and repair and then using System Restore to return to an earlier checkpoint. A checkpoint created before the presentation software was installed…Ron shook his head and started the Help Desk 101 questions. “Do you shut down the system when you’re packing up?â€â€œOh, we just turn the generator off,†the grunt answered. “That shuts everything down.â€Ron mentally facepalmed. “You need to properly shut down the system before killing power or this will happen again.†He went inside the trailer and showed them a power button on the control panel. The button was just wired to the power switch header on the PC’s motherboard and acted exactly like any computer case’s power button. Pressing it briefly tells the operating system to shut itself down. “Just press this button and it will shut itself down in a minute or two.â€â€œOkay, that’s simple enough,†the grunt said.Then Ron spent the day re-installing and configuring their system by downloading all the software over his phone’s mobile hotspot to his laptop, then transferring it via USB stick. Eventually he had it back up and running. He made sure to stress how important it was to shut down the system, and on a whim left them a DVD with all the software so he could talk someone through the process over the phone if it happened again.He returned home. And two weeks later, it happened again. He spent three days on the phone talking to a different grunt and walking him through restoring the system. Again he emphasized the importance of shutting down the system with the power button before killing power, but this grunt explained he did that. Ron was confused, but finished the support call.Just a few days later, they called again. He talked to yet another grunt, asked them how shutdown was handled, and he explained he pressed the button until it shut down. His boss decided to send Ron on-site again, and he repaired the system. It was much faster this time since he had a DVD with everything he needed on it, only taking most of a morning. When he was done, he tested the power button. It shut down the system properly.“Show me how you get ready for a presentation,†he asked. “From setup once you’re on-site, to shutdown.â€The pair of grunts assigned to him–two more he’d never worked with before–spent an hour walking through the process. When they got to the end, Ron reminded him to shut down the system.And the grunt did so. By pressing and holding the power button for about five seconds. Which killed power to the PC without properly shutting down the operating system.He mentally facepalmed again. “No, you can’t press and hold. Just tap the button. It will eventually shut down.†He was getting fast at restoring the system and spent that afternoon correcting it all. This time he took a System Restore snapshot once everything was in place, and taped a hand-written note on the control panel saying “DO NOT HOLD THIS BUTTON TO TURN OFF THE MACHINE. DO NOT SHUT OFF THE GENERATOR WITHOUT FIRST TURNING THE SYSTEM OFF PROPERLY.â€He returned home. And a couple weeks later, they called again. He was unable to fix it over the phone and was sent on-site yet again. This time the filesystem was too corrupted to repair and he had to set everything up from scratch. Upon querying the new grunts he discovered they ignored the note and were still holding the power button to kill the system.This continued for a couple more months. The client refused to shut down the system properly and was constantly causing severe filesystem corruption or even killing hard disks. Each time the client called, getting angrier and angrier. “It says there is no OS! I thought you fixed this bug!!†Each time the problems were caused by operator error.During a meeting with his boss Sam, Ron explained all the issues and how much of his time it was taking, and while brainstorming a solution Ron pitched a new idea. “What if we modify the custom power button? Alter it to only send a pulse, instead of a constant closed signal, so it’s impossible to hold it down?â€â€œFigure it out and do it,†Sam ordered. “These guys are idiots and won’t do things right. They’re killing us on support time, we have to fix this or fire the client. How hard is it to shut this thing down properly?â€So, being a software engineer, Ron devised a clever solution based on an Arduino that sampled the power button’s state and sent pulses to the motherboard’s power button header. It passed all his testing and he went on-site to install it. And finally the support calls ceased completely. This unit was the only one that received the update since none of their other clients had issues with operator error.With the issue solved, Ron decided to take some badly-needed vacation to attend a family reunion in North Carolina and tried to stay off the grid. Meanwhile, Sam took a demo unit to an expo in London so visitors could smell what it was like to go skiiing.During his vacation, Ron received a phone call from Sam in the middle of the night. Being on vacation and trying to stay offline, he ignored it. But the phone rang in quick succession several more times and he finally answered.“Ron! Sorry to wake you, but our demo unit quit working and I need your help!â€Ron grunted. “It’s one AM here…â€â€œI know but I need to get this back up before the conference starts this morning!â€â€œOkay,†he said with a sigh. “What’s it doing?â€Sam proceeded to describe a series of error screens over the phone. It stated that “Windows was not shut down properly,†followed by a long filesystem scan, followed by an error that critical system files were corrupted and Windows could not boot.Ron facepalmed for real this time. [Advertisement] Universal Package Manager - ProGet easily integrates with your favorite Continuous Integration and Build Tools, acting as the central hub to all your essential components. Learn more today!
 |
by Remy Porter on (#2PRZD)
Last week, I shared some code that, while imperfect, wasn’t that bad. I then issued a challenge: make it worse. Or better, if you really want. As many comments noted: one case covers only the first iteration of the loop, and one case only covers the last iteration of the loop. You could easily pull those out of the loop, and not need a for-case at all. Others noticed that this pattern looked like odd slices out of an identity matrix.With that in mind, we got a few numpy, Matlab, or MatrixUtils based solutions generally were the “best†solutions to the problem: generate an identity matrix and take slices out of it. This is reasonable and fine. It makes perfect sense. Let’s see if we can avoid making sense.I’ll start with Abner Qian’s Ruby solution.
|
 |
by Jane Bailey on (#2PMQG)
She'd resisted the call for years. As a senior developer, Makoto knew how the story ended: one day, she'd be drafted into the ranks of the manager, forswearing her true love webdev. She knew she'd eventually succumb, but she'd expected to hold out for a few years before she had to decide if she were willing to change jobs to avoid management.But when her boss was sacked unexpectedly, mere weeks after the most senior dev quit, she looked around and realized she was holding the short straw. She was the most senior. Even if she didn't put in for the job, she'd be drafted into acting as manager while they filled the position.This is the story of her first day on the job.Makoto spent the weekend pulling together a document for their external contractors, who'd been plaguing the old boss with questions night and day— in Spanish, no less. Makoto made sure to document as clearly as she could, but the docs had to be in English; she'd taken Japanese in high school for an easy A. She sent it over first thing Monday morning, hoping to have bought herself a couple of days to wrap up her own projects before the deluge began in earnest.It seemed at first to be working, but perhaps it just took time for them to translate the change announcement for the team. Just before noon, she received an instant message.Well, I can just point them to the right page and go to lunch anyway, she thought, bracing herself.Emilio: I am having error in application.
|
 |
by Remy Porter on (#2PGM1)
There’s a lot of debate about how much a developer should rely on comments. Clear code should, well, be clear, and thus not need comments. On the other hand, code that’s clear the minute you write it might not be as clear six months later when you forget what it was for. On the other, other hand, sometimes a crime has been committed and we need the comments for a confession.Austin S confesses his crime.
|
 |
by Mark Bowytz on (#2P6ZV)
"What do you think the buttons do? If you thought the dialog was trying to help you log in or give an opportunity to send them an e-mail, instant message, or tweet pointing out how the buttons don't do anything, you might be mistaken," writes Alex M., "
|
 |
by Jane Bailey on (#2P302)
As many of you know, outside of being a writer, I also work on open-source projects. The most famous of these is Sockbot, a chatbot platform that interfaces with various forum and message clients. If you're reading this, my boss didn't object to pointing out that my work has never made this particular mistake—but maybe we'd be more famous if we had.This particular chatbot was designed for internal use. The company, like many others, had moved to Slack as an IM program for their development teams. Like every other team that found themselves with a slack, the developers quickly set about programming bots to interact with the platform and assist with common tasks like linking to an issue in the company Jira, pushing out a docker container to the QA environment, and ordering lunch.Today's submitter, Suzie, wanted to add Google search to her local bot, Alabaster. Often, when people started talking about something, they'd grab the first link off Google and dump it into the chat for context. This way, Alabaster could do that for them. Sure, it wasn't the most useful thing in the world, but it was simple and fun, and really, isn't that why we program in the first place?Of course, Google puts a rate limit of 100 queries per day on their searching, and you need an API key. Bing, on the other hand, had a much higher limit at the time of 5,000 queries a month, and was much easier to integrate with. So Suzie made the executive decision to settle for Bing and eat the gentle razzing she'd get in response.If you've never used a chatbot before, there's two ways to design them. The harder but much-nicer-to-use way is to design a natural language processor that can tell when you're talking to the bot and respond accordingly. The easier and thus far more common way is to have a trigger word and a terse command syntax, like !ban user to ban a user from the chat room. Command words are typically prefixed with a bit of punctuation so they can't accidentally be used to start a sentence, too. In the example I gave, the ! informs the bot that you're talking to it, and ban is the command, given the argument user to the command handler.Alabaster was using !! as his trigger, so Suzie settled on !!bing as the bot command to start a search, passing in the rest of the line. Since she wasn't using Sockbot, she had to handle the line parsing herself. She went the easy way and replaced the first instance of the word "Bing" with empty space before handing the rest of the line to the Bing API.Or ... she tried to. In reality, she wrote var searchText = message.TargetedText.ToLower().ReplaceFirst("big ", "").Trim();, missing the all-important "n" in "bing".This wouldn't usually be a big deal. If you start your Google search phrase with the word "google", it's usually ignored while Google searches for the rest of the phrase. Bing, however, is also part of several people's names, such as Bing Crosby, Chandler Bing ... or porn star Carmella Bing, the most searched of the three. Somehow, Suzie had also allowed the searches access to NSFW results. Every time Alabaster was asked to search, it came back with X-rated results about the porn star.Suzie scrapped the module and started over. This time, she decided Google's rate limit was probably just fine ... just fine indeed. [Advertisement] Application Release Automation for DevOps – integrating with best of breed development tools. Free for teams with up to 5 users. Download and learn more today!
|
 |
by Remy Porter on (#2NZ1Z)
So, fun fact about myself: I didn’t know what the For-Case anti-pattern was until relatively recently, when there were a spate of articles condemning it as an anti-pattern. I’m sure I’ve probably used it, at some point, but I never knew it by name. It’s thought of as a textbook antipattern that generally implies a misunderstanding of for loop, case statements, the problem being solved, or some combination of all three. That said, there are certain problems that might be more clear to solve by using the For-Case. Like GOTO, it might be harmful, but its actual evil exceeds its reputation.John A had a problem, and most unfortunately for him, this problem involved VBA macros embedded in an Excel spreadsheet. He needed to generate four arrays, that fall into this pattern:
|
 |
by Remy Porter on (#2NVQF)
|
 |
by Remy Porter on (#2NV4N)
It was a particularly irritating Monday morning, when Travis got a frantic text from his boss. The sun was shining, the birds were nattering, and everyone was greeting him with a smile; it was like everyone in the world had their coffee, but Travis overslept and was going to have to satisfy himself with whatever sludge he could scrape out of the office coffee maker. He had just crossed the threshold when the text arrived:
|
 |
by Remy Porter on (#2NQBR)
If you want to send emails from a Java program, you might be tempted to use the javax.mail package, which contains objects for doing exactly that. It’s a relatively straightforward API, and while it’s a bit verbose, that’s hardly unusual for Java. You just wrap it up in a convenience function based on how you need to call it, and reuse that, right?Well, PHP, an obviously superior language, already did that work. There’s a built-in mail function, which sends emails. It uses your php.ini file to figure out what SMTP service to use, making the parameters to the function more “obviousâ€.Chris had a co-worker that really loved the… elegance… of PHP’s solution to this problem, and thus, when they needed to send emails from Java, they did it this way:
|
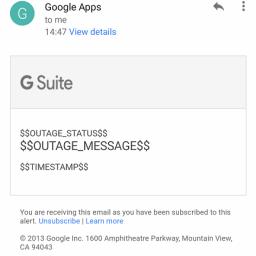 |
by Mark Bowytz on (#2NE41)
"When Google's having an outage, and it's also affecting their outage notification service, things are NOT going well" writes Nathan.
|
 |
by Remy Porter on (#2NACR)
Have you ever fallen asleep on your keyboard? Aside from the awkward face-prints it leaves behind, did you notice yourself programming in your sleep? I suspect that Chris’s co-worker does sleep-program. At least, that’s the only explanation for the 7,088 line code-sample I’m about to show you. Don’t scroll too fast- there’s actual code mixed into the middle of this. And yes, I’m including all of the code.Which is less than you’d think, from the line count.
|
by snoofle on (#2N6DX)
 |
by Remy Porter on (#2N2B9)
Pearl’s employer couldn’t find an off-the-shelf product that handled their call-center needs, so they developed one in house. One department didn’t want to use that front-end, so they developed a different one in house, but it still used the same backend… mostly. Another group did the same thing, adding some fields and extending the database. And then another. Then there was an organizational restructuring, and suddenly the call-center reps found themselves in the annoying position of needing to do double- or sometimes triple-entry, in order to get all the right columns and fields filled out based on the current business rules.Now this is a textbook example of where one might want to engage in some business process improvement: identify the actual needs of the organization, and implement software suited to those needs (chucking out any legacy kruft that you don’t need). Doing this, of course, takes some work, it takes some analysis, and it takes an organization willing and ready to make changes.Pearl’s organization was not ready and willing to make changes. Instead, one of the PHBs had recently read an article on “robotic process automationâ€, which is a fancy way of saying, “we’re gonna screen-scrape using a fancy drag-n-drop workflow tool.†Instead of spending time and money training the in-house developers to use the tool, the company could outsource it to a much cheaper team that already had experience.Now, one-size-fits-all drag-n-drop scripting usually fails on the difficult edge cases, and Pearl’s company had lots of difficult edge cases. No problem, the offshore team could just write some C# scripts to do the job, and call them from the workflow tool.This is the script CheckFallingDate.cs which does… something.
|
 |
by Jane Bailey on (#2MYP2)
It was early in Seth's tenure at PicoServices Inc. when he first heard about Joe."Oh, man," he was told by a coworker he'd recognized as having a good head on her shoulders. "I can't wait until you end up at a Joe review.""Joe? Why's that?" he asked, tilting his head."Nope, no way. You get to experience Joe the hard way."Over the coming week, Seth was pretty sure he'd caught people taking bets for something to do with the coming code review, but he wasn't sure why. Joe had seemed like a reasonable fellow when they'd reviewed Beth's code together, and he'd had a few useful pointers for Seth about how to talk to one of their project managers. What could be so bad?When he got to the conference room where the team had gathered to review Joe's new code, Beth beckoned him over to sit by her, right at the base of the U-shaped table where he had a prime view of the projector. As Joe got his laptop plugged in, most of the room seemed to be watching Seth's face with varying degrees of subtlety.Oh ... kay ... Seth thought, bracing himself for some weird hazing ritual.Then the projector flickered to life, and he settled in to read the function.
|
by Mark Bowytz on (#2MMK1)
"If you want to sneak in an ad that doesn't necessarily belong in Kongregate, I guess a little creative spelling is one way to do it," wrote Ben J.