|
Gang has cunning way of hiding itself by using multiple names Suspected hackers based in India have compromised thousands of computers, going about their business as far back as 2013.…
|
Story
The Coming Internet-Of-Things Horror ShowSimilar News
by Paul Karp from on (#1Q0ZM)
Bureau of Statistics and government deny cyberattack took place, instead blaming it on a ‘confluence of events’The federal government and Australian Bureau of Statistics (ABS) have explained the outage of the online census was the result of a systems failure and an “overcautious†response to a denial of service attack.At a press conference on Wednesday to explain the outage since about 7.30pm on Tuesday, the small business minister, Michael McCormack, blamed the failure on a “confluence of events†but said the system had not been breached and no data was lost. Continue reading...
 |
by Darrell Etherington from Crunch Hype on (#1PYZV)
Kepler Communications has raised $5 million in seed funding to create a network of small, easily replaced satellites to create a real-time network through with internet of things (IoT) devices can communicate, essentially building a cellular network in space through which machinery and equipment can talk to one another and to its handlers. “You can think of it as a cell phone tower… Read More
|
 |
Kashmir Hill is asking an interesting question over at Fusion: in the wake of Democratic National Committee email hacking, will political leaders start scaling back their war on encryption?
|
 |
by Natasha Lomas from Crunch Hype on (#1PV1S)
Privacy rights organization Privacy International has filed another legal challenge to the UK government’s use of bulk hacking against foreigners. The filing, with the European Court of Human Rights, follows Privacy International’s attempt earlier this year to challenge the use of bulk hacking against foreigners via the local oversight court for the UK’s intelligence… Read More
|
 |
from heise online News on (#1PPAX)
Auch Privacy International und andere Organisationen haben jetzt in Straßburg Beschwerde eingelegt gegen die Internet- und Computerspionage des britischen Geheimdiensts GCHQ. In London waren sie zunächst nicht erfolgreich.
|
Windows 10 IoT Core for the Raspberry Pi Is Now Easier to Set Up, Adds Remote Client Access and More
by Thorin Klosowski from Lifehacker on (#1PM96)
Windows 10 on the Raspberry Pi is a great way to create your own internet connected devices , and today Microsoft pushed out an update that makes the set up process a bit easier.
from Hacker News on (#1PJMT)
Comments
 |
by LXer from LinuxQuestions.org on (#1PHKW)
Published at LXer: In a talk at the Embedded Linux Conference, Mike Anderson, CTO of The PTR Group, explored the unique security challenges that face Linux-based IoT devices. Read More......
|
 |
by Kate Conger from Crunch Hype on (#1PG3B)
During what was likely the first presidential campaign fundraiser held at the Black Hat security conference in Las Vegas, campaigners made their case for Hillary Clinton as the cyber candidate.Last night, Jeff Moss, the founder of Black Hat, and Jake Braun, a former Obama campaign staffer and security consultant to the Department of Homeland Security, pitched Clinton to the security pros… Read More
|
 |
by LXer from LinuxQuestions.org on (#1PESJ)
Published at LXer: myDevices announced Arduino support for its web- and mobile-based, Raspberry Pi compatible “Cayenne†drag-and-drop IoT development and management platform. Cayenne, with which...
|
 |
by Tekla S. Perry from IEEE Spectrum on (#1PC27)
ConnectedYard is the kind of company that could only have been cooked up at a backyard barbecue in Silicon Valley
|
by Cyrus Farivar from Ars Technica - All content on (#1P9K3)
Oregon Supreme Court: Woman stole, but she was "authorized" to use lottery machine.
 |
by Ben Dickson from Crunch Hype on (#1P8VE)
As the Internet of Things evolves into the Internet of Everything and expands its reach into virtually every domain, high-speed data processing, analytics and shorter response times are becoming more necessary than ever. Meeting these requirements is somewhat problematic through the current centralized, cloud-based model powering IoT systems, but can be made possible through fog computing. Read More
|
 |
by Andy Greenberg from on (#1P5YE)
After sparking a 1.4 million vehicle Chrysler recall, the security researchers offer a new lesson: It could have been---and could still be---much worse. The post The Jeep Hackers Are Back to Prove Car Hacking Can Get Much Worse appeared first on WIRED.
|
 |
Controlling human nerve cells with electricity could treat a range of disease including type-2 diabetes, a new company says.
|
 |
from Hacker News on (#1P2VV)
Comments
 |
by LXer from LinuxQuestions.org on (#1NXGX)
Published at LXer: Well, it's about time. People are finally realizing how easy it would be to hack an election - assuming it hasn't happened already. Read More......
|
 |
by Cade Metz from on (#1NR93)
The contest next week will be a true test of how well software can protect software. If the bots succeed, they could transform the way cybersecurity works. The post Security Bots Will Battle in Vegas for Darpa's Hacking Crown appeared first on WIRED.
|
 |
from The World: Latest Stories on (#1NPJ6)
Donald Trump held a news conference in Miami in which he called on Russia to find Hillary Clinton's missing emails. So what does the former US ambassador to Russia think of Trump's comments?
|
 |
by LXer from LinuxQuestions.org on (#1NKY0)
Published at LXer: RTL has published a tutorial about creating a secure IoT platform based on its free “SharkSSL-lite†software, plus ARM mbed-enabled SBCs and a low cost VPS. Real Time Logic...
|
by Samuel Gibbs from on (#1NHAR)
Hackers deface technology site while telling visitors attack is only a security test in latest high-profile breachVerizon-owned prominent technology site TechCrunch has become the latest victim of the OurMine hacking group.
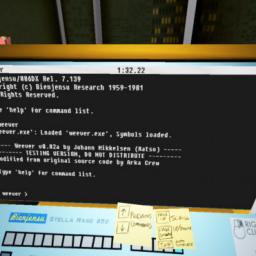 |
by Jake Muncy from on (#1NH3B)
The new PC game "Quadrilateral Cowboy" is a love letter to '80s cyberpunk and collaborative creation. The post Hacking Game Quadrilateral Cowboy Is a Bit Messy, But You Won’t Forget It appeared first on WIRED.
|
 |
by LXer from LinuxQuestions.org on (#1NFBX)
Published at LXer: The ArchStrike developers have announced today that their Arch Linux-based operating system designed for ethical hackers now has official installation mediums as ISO images. ...
|
by ORF Online und Teletext GmbH & Co KG from news.ORF.at on (#1NEB4)
 |
by Jennifer Baker from Ars Technica - All content on (#1NE7T)
US officials want Love to face charges of hacking NASA, the FBI, and the US Army.
|
 |
by Cory Doctorow from on (#1NE27)
Bruce Schneier warns us that the Internet of Things security dumpster-fire isn't just bad laptop security for thermostats: rather, that "software control" (of an ever-widening pool of technologies); interconnections; and autonomy (systems designed to act without human intervention, often responding faster than humans possibly could) creates an urgency over security questions that presents an urgent threat the like of which we've never seen. (more…)
|
 |
 |
by Thane Kreiner from Crunch Hype on (#1N5X6)
In Silicon Valley the term “hacker†has evolved to connote high praise for someone particularly creative, ingenious and adept at finding clever new ways to accomplish a difficult task. And it’s with that framework in mind, rather than some of the other meanings that “hack†has represented over time, that I suggested during my recent TEDx talk that Pope Francis and… Read More
|
 |
Sentencing set for September Five men working at UK-based IT security reseller Quadsys confessed today to hacking into a rival's database.…
|
 |
by Brian Heater from Crunch Hype on (#1N19D)
When he was seventeen, George “geohot†Hotz became the first person to jailbreak an iPhone, back when Apple really didn’t take too kindly to such things. Three years later, he moved his unlocking efforts over to the PlayStation 3. Again, Sony wasn’t feeling it. The young hacker has since joined forces with a number of high-profile tech corporations, first at… Read More
|
 |
by LXer from LinuxQuestions.org on (#1MZ4P)
Published at LXer: Onion launched an [he]#8220[/he]Omega2[he]#8221[/he] module on Kickstarter, featuring a faster CPU, options for double the RAM and flash, and lower pricing than last...
|
 |
by LXer from LinuxQuestions.org on (#1MXDQ)
Published at LXer: In this interesting ELC video, Grant Likely, a Linux kernel engineer and maintainer of the Linux Device Tree, describes his journey into embedded hardware. Sometimes the best...
|
 |