 |
by snoofle on (#4EPWJ)
When I was in college, as part of the general course requirements we had to take Probability and Statistics. The first time around I found it to be an impenetrable concept beyond my grasp, and I flunked. Since it was a requirement, I took it again and barely skated by. Joy; I had cleared the hurdle!By that time, it had become clear to me that I was going into a field that required a whole lot more understanding of P&S than I had acquired. Since I wanted to be properly prepared, I signed up for a free summer school course to try it once more.This time, the professor was a crotchety old German mathematician. He would not allow us to record the lectures. We were told not to bring the textbook to class as the turning of pages distracted him. We were not even allowed to take notes. Every class began with Good morning, Pencils Down! He firmly believed that you had not mastered a skill unless you could explain it in simple words to a complete neophyte, by merely describing it in non-technical terms that they already understood.Based upon my prior two attempts at this subject, after two classes I was convinced that this was going to be a waste of time. After all, if I could barely understand it with the textbook and notes, what chance did I have like this? But I had already signed up and committed the time, so I stuck with it.To my shock-surprise-awe, he managed to verbally paint a picture through which the concepts became crystal clear; not just to me, but to everyone in the class. I had no trouble acing all the homework assignments and tests, and my entire notebook for the course consisted of:
|
 The Daily WTF
The Daily WTF
| Link | http://thedailywtf.com/ |
| Feed | http://syndication.thedailywtf.com/TheDailyWtf |
| Updated | 2026-06-04 19:45 |
by Remy Porter on (#4EMCP)
C# has always had some variation on “string interpolationâ€, although starting in C# version 6, they added an operator for it, to make it easier. Now, you can do something like $"{foo} has a {bar}", which can be a very easy to read method of constructing formatted strings. In this example, {foo} and {bar} will be replaced by the value of variables with the same name.C#’s implementation is powerful. Pretty much any valid C# expression can be placed inside of those {}. Unfortunately for Petr, that includes the string interpolation operator, as a co-worker’s code demonstrates…
by Remy Porter on (#4EJ4Z)
Let's simply start with some code, provided by Adam:
by Mark Bowytz on (#4ED4C)
"When I ordered on Hasbro Pulse's site, I don't remember paying using a large sandwich, but...here we are," writes Zeke.
by Remy Porter on (#4EAR4)
A not uncommon pattern is to use a dictionary, or array as a lookup table in place of a switch or conditional. In some languages, like Python, there is no switch statement, and dictionaries are the main way to imitate that behavior.In languages like JavaScript, where the line between objects and dictionaries is blurred to the point of non-existence, it’s a common approach. A lot of switch statements can be converted to an object literal with functions as its values, e.g.:
by Remy Porter on (#4E8BA)
"Procedures should be as small as possible," is good advice. Like any good advice, you can take it too far.Mike recently was asked to upgrade a SQL Sever 2000 database to SQL Server 2016. Since this was an upgrade, Mike wasn't supposed to make any changes beyond the necessary changes to make the upgrade work. Still, when he found a bunch of methods with the same basic naming pattern, he had to investigate.
by Remy Porter on (#4E5XZ)
Myrtis joined Initech as their first on-staff software developer. Up to that point, Initech outsourced all the software development on their payroll/billing system. The contractor kept raising their rates, Initech’s business needs kept growing, and eventually they decided it was time to hire an in-house developer.Which meant Myrtis got to inherit all of that outsourced development. All that code, all of which had some pretty significant financial implications if it contained any bugs or errors, all developed by a third-party to a third-party.Imagine, for example, that you need to round to the nearest quarter. That is to say, 1.12 rounds to 1.00, while 1.19 rounds to 1.25.
 |
by Jane Bailey on (#4E3NB)
Sometimes the writing is on the wall; sometimes, you know you have to get out. Today's submitter, Pietyr, was in just that sort of situation. He decided to head for greener pastures, hoping for a job with a good atmosphere, someplace where he could take it easier and enjoy his work more.Initech was a startup, one that didn't have any clients yet. No external deadline pressure, just venture funding and free beer Fridays. Pietyr gave them a call and spoke with their receptionist-who-was-also-HR, Chrysanthemum."May I call you Chrissy?" he asked, trying not to laugh."You can call me anything you like, Sugar, so long as it's not 'late for dinner.'"Pietyr scored an interview same day—"Come on over when you get a chance, darling, we're here all afternoon"—and so, at 4:00, he called off for a doctor's appointment and drove to the site. It was a suite in a larger building, all one dim room, lit mostly by Christmas lights ... in March. A dozen people crowded onto long tables, plugging away at MacBooks, entirely uninterested in his arrival. While Chrissy answered phones, he watched a good ten minutes of Kindergarten Cop on the large TV they clearly had on for white noise in the background.At least it's different, he told himself."Mr. Taberd will see you now," Chrissy said, interrupting Arnold."Ah, right. And that is ...?""The CTO."With no further preparation than that, he was ushered into a side room, little bigger than a closet, into which a lean blond man and a midsize desk had been crammed unceremoniously. He shook hands, sat, and let the CTO do most of the talking."What's the biggest issue with cloud computing?" Mr. Taberd finally asked, leaning forward."Security?" guessed Pietyr."Wrong! It's monitoring. When you don't have access to the servers, you don't know what they're doing! But that's where Initech comes in," boasted the blond, in what was clearly a prepared elevator pitch. "Windows is always doing things under the hood, and it's impossible to tell what at scale. Not without a centralized system. What we're doing here is hooking the Windows API calls—""Which ones?""All of them! Every API in the user, gdi, and networking DLLs, plus some of the internal kernel functions. We hook them through a backdoor my boys have cooked up, save off all the parameters whenever they're called. Our background process reads those parameters from shared memory, ships them to a cluster of databases—we're doing about 250 elastisearch instances per server—and reads it all into our responsive web frontend. That way you know exactly what it's doing at all times!"Pietyr could tell right away it would never work. Not even in Windows XP, let alone more secure versions. Too much overhead; it would bring the monitored server to its knees.But, on the other hand, free beer. And hey, if the product never sold, he could kick back and take it easy, right? As soon as Tabard mentioned free lunch every day—"Thanks to our Venture Capital funds!"—he was in.He took the job, working on the low-level hook code so that all the cloud nonsense was someone else's problem. A month later, he received a letter informing him his shares were effectively worthless. Fine by him, since he had no shares anyway.It took another month before he casually asked a coworker how long they'd been working there."Oh, not long. Only about two years.""Really? You must have been here since the beginning then, or nearly," Pietyr commented. He would have guessed from the codebase the company had only been running six months or so, but he kept that to himself."No, no. Jan has been here all seven years, I've only been here two."Pietyr stared. "Seven years?! You've been working on this with no customers for seven years?!""Well, I heard a rumor we've got a client about to sign up for the beta.""A rumor." Pietyr sighed, firmly placing the conversation in the not-my-business bucket, and got on with his work. Still, the sense of unease didn't leave him.A month after that, the unthinkable happened: Taberd not only left his little office, but turned off the television. "Alright, everyone, listen up! Stop what you're doing. We're out of money."And just like that, Pietyr was back on the job market. That day, he learned a valuable lesson: don't let free beer convince you to ignore red flags. [Advertisement] BuildMaster allows you to create a self-service release management platform that allows different teams to manage their applications. Explore how!
|
by Mark Bowytz on (#4DYCT)
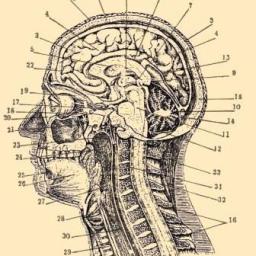
"Behold how TDWTF commenters get their start in life!" Adam G. writes.
by Remy Porter on (#4DVTH)
Tom C inherited some Go from another developer, and writes, “I’m pretty sick of finding this sort of stuff in this code.â€
by Remy Porter on (#4DSAY)
Web development has gone in a bizarre circle since the early 2000s. Whet ASP.NET launched, its “big sell†was Web Forms, which allowed developers to use a desktop model for handling interactive applications. The basic logic you used for building a desktop forms application would work for a web app, because at the time, everyone was a desktop developer.Fast forward to today, where we bundle our applications up in web browsers and use web metaphors to build desktop applications, because everyone’s a web developer. This may be proof that developers can only ever learn a single way of doing things, and that two options is one too many.Which brings us to some code Petr Tomanek recently inherited. The original developer, Josiah, started their career around the early 2000s. They were big advocates of the data row approach to data access. In code, they’d forget that they’d already run a query, and run it three more times just to be sure to get the data. Their approach to UI wasn’t even quite up to Web Forms standards, and was more, “mash together my personal library of snippets and Stack Overflow copy/pasteâ€. The current incarnation of the application used the more modern ASP.NET MVC, but you wouldn’t know it to look at most of the code.But Josiah would at least try to use the new features. For example, when they wanted the URL of a screen in the MVC application, they knew that the ActionLink method was how you created links in your view. There was also a Url.Action method which would construct just the URL. But that’s two different ways to do something, and that’s one too many. Josiah did this:
 |
by Ellis Morning on (#4DPWN)
Not so long ago in 2015, Carl C. was asked to give a talk to an amateur radio club. The venue was a local church that rented out their meeting hall to various community groups, businesses, and even the odd academic session. The space boasted a multimedia setup with several video screens, making it a great place at which to present.Carl prepared his talk, and a PowerPoint slide deck to go with. On the day of the presentation, he arrived at the meeting hall with plenty of time to spare. Alone in silence, he headed toward the front of the room and surveyed the technical setup. Thankfully, it was straightforward: there was a table set up in front of the projector screen, with a VGA connector resting directly on it. Carl unpacked his laptop, retrieved the HDMI-to-VGA adapter he'd brought along, and began plugging everything together."NOOO!"Carl jumped, then glanced up wide-eyed like a deer in headlights. It wasn't a truck bearing down on him, but rather a flustered gentleman hugging a laptop to his chest."I'm the IT guru here," he introduced himself breathlessly, hurrying around the table to all but elbow Carl aside. "We don't allow outside computers to be connected to our system. That's how viruses spread! You'll have to run your presentation from our computer." He connected his own laptop to the AV system in lieu of Carl's."Uh ..." Carl blurted."Yes?" The guru fixed him with a withering stare.I'm not joining your network, Carl thought. There's no such thing as VGA viruses! But the stare was so intense that the objections died before they left his throat."How, uh ... how do I get my presentation on there?" he asked instead, gesturing to the guru's laptop."Can you copy it to a USB stick?" the guru asked. "That's the best way."Right. No one's ever gotten a virus from a random USB stick. Biting his lip to short-circuit a laugh, Carl dug through the side pockets on his laptop bag. "I think I've got one with me." [Advertisement] Forget logs. Next time you're struggling to replicate error, crash and performance issues in your apps - Think Raygun! Installs in minutes. Learn more.
|
by Remy Porter on (#4DMT4)
Ben M recently inherited some code from some Highly Paid Consultants. These consultants needed to be able to set some flags to control the behavior of the application, and for whatever reason, these flags needed to be strings. It probably wasn't a good reason, but there was some reason. The consultants wrote the module which set the flags, and guaranteed that the flags were only ever "true" or "false".To parse those flags back into boolean values, they did it the true Highly Paid Consultant way: they used a generic "string to boolean" solution they copied from Stack Overflow instead of Boolean.Parse, the built-in C# method for turning "true" into a boolean value.
by Mark Bowytz on (#4DFTT)
Gordon S. wrote, "In seeing how someone botched the deployment of Windows on the flight boards, I sure hope that's ALL that admin was allowed to work on."
by Remy Porter on (#4DDFE)
There are many moments where our multi-threaded code needs to gurantee only one code path is executing at a time. That’s why we have locks, semaphores, mutexes, and so on. But those are all pretty complicated. Vincent H recently was reviewing someone’s code, and they found a far more elegant solution, which simply uses booleans.For example, you could whip up a wait loop with a simple block like this:
 |
by Charles Robinson on (#4DAZE)
Alvin had the fortune of working with an exceptional talent while he was employed at Virtucon. Bart knew how to do everything from desktop support to software development to database administration to IT security. Not only was he proficient in all of them, he also knew them better than those with many years of experience.Bart had been with Virtucon since the early days, racking up nearly 20 years of tenure. During this time, he 'mastered' everything and asserted himself to the point that no changes could happen without his approval. His changes were auto-approved because of course any idea he had was a good one. This led to myriad problems for fellow IT people like Alvin, who were hired after Bart."Be wary of Bart," Alvin was warned by his coworker Bob, who was Bart's junior by a couple years. "He has a long history of buffoonery, yet has somehow ascended to the #3 position in IT." Alvin sipped on a generous mug of coffee while Bob regaled with the Ballad of Bart. From the time he was just a helpdesk intern that put his shoulder through a core switch after tripping while carrying boxes, Bart was wrecking things.When Bart worked his way up to server support, he 'fixed' an Exchange issue by restoring a backup into production without warning because "It worked when the backup was taken." When he was assigned a web server problem, he spent a few days troubleshooting it without asking for any help. When he finally gave in, he told Bob that he couldn't figure out a frustrating IIS HTTPS binding issue. Bob explained to him that something else had to be the problem because the server was running Apache 2.4 on Ubuntu 16.04 LTS.When Bart added software development to his repertoire, he clearly didn't understand how code changes worked. Or code repositories for that matter. He always wanted to be the one to fix problems, so he would stick his nose in code that it didn't belong.Bart once tried to make fee schedule changes to accounting software by opening its PowerBuilder libraries in Notepad++. He proceeded to print out the .PBL and use a pencil to scribble out every value from the old schedule and wrote in the new ones. He then scanned his penciled changes in as a PDF and emailed it to Bob to implement.Frustrated, Bob spent an entire day showing Bart how their GitHub repositories worked. He seemed to understand, so Bob went on his way. While Bob hoped Bart wouldn't actually produce any more code, perhaps it would save their printer some toner if he did. The next day, all the developers were complaining to Bob that they couldn't access GitHub. It turns out Bart saw GitHub as a threatening malicious code breeding ground so he had a network admin block it on the firewall. He then sent an email to development staff explaining this and that they were supposed to now use 'BartHub', a file share he set up on his own computer.Bob and the developers managed to distract Bart by pointing out how the DBA team needed help. The first thing he did was try to create an SSRS report using a series of text boxes in a grid to make a matrix. The DBA's had a good laugh at that until Bart started to commit worse atrocities.One day an entire metrics database suddenly became a bunch of null values, which is not very helpful for metrics. Bart threw a fit because the data he was working on was gone. He demanded whomever messed up the data be hunted down. He suggested that missing historical data could be found by performing 'key triggers', whatever those were. He emphasized his point by making hand motions like he was scrambling a Rubik's cube. They ignored him and a lead DBA ran a profiler trace to find that the unconstrained null updates came from... Bart's workstation.Alvin had long since imbibed his coffee when Bob finished his story. Bob turned back to his workstation to check his email, "Oh, would you look at that. I guess we have some changes up top!" The email stated that the current VP of IT was announcing his retirement after 30 years at Virtucon. The CTO would be taking on that new role at the end of the month.The transition plan began and the CTO was groomed to take over. That plan was shredded a week before it was to take place because the CTO suddenly found himself unemployed. The finance department was investigating his use of the company credit card and found thousands of dollars in personal charges, so he was unceremoniously terminated. Turmoil gripped the office as an entire department waited to find out who their new leader would be.Everyone except Bart put in a good word for Bob to become the next VP of IT. At minimum, they should hire someone from the outside. Pretty much anyone but Bart was the popular suggestion.Bart predictably put in a good word for himself and talked a big game about all of his expertise. He added security expert to his resume by talking about disabling his home WIFI’s SSID broadcast and changing the default password. Then there was the previously-unmentioned experience as an IT Project Manager where he apparently led several teams at Schmoeing.That Friday, that dreaded email with the subject New VP of IT came out. Being the most tenured person remaining while having "great leadership qualities," Bart got the promotion and Bob didn't. Many job search sites probably thought they were getting a DDoS attack over the weekend while everyone in Virtucon IT looked to abandon ship. Bart's reign of terror lasted 18 months before Virtucon realized they made a grave mistake. Bob, Alvin, and many others weren't around to see the way it all ended. [Advertisement] Forget logs. Next time you're struggling to replicate error, crash and performance issues in your apps - Think Raygun! Installs in minutes. Learn more.
|
by Remy Porter on (#4D8JB)
We all just love ternaries around here. So much. A powerful form of code golf, they can clarify and they can confound, but usually it’s just confounding.Christopher sends us this example, saying, “This is an accurate indicator of the rest of the code.â€
by Remy Porter on (#4D64M)
Today, any sort of data access layer we build is going to be rooted in some sort of object-oriented design. It might be a full ORM, it might be an object-store database, it might be one of any number of kinds of database mapping tool.What we usually don't do anymore is get a resultset with no type information, where we have to invoke the proper "GetXXX" method to fetch data out of what behaves more-or-less like a dictionary. Oh, we might have to do this, but we'll almost always bury it under a layer of abstraction to hide the ugly details.I bring this up because once upon a time, this was pretty standard stuff. Result sets and data readers were just how you talked to databases. It's old fashioned, but not wrong.Russell F recently had to add some new fields to some code written in that style. This was wrong.
by Mark Bowytz on (#4D0P2)
"Does this mean that Toyota believes that hybrid owners are fundamentally unhappy with their cars?" writes Thom.
by Remy Porter on (#4CY4Q)
Kids these days have their flexboxes and their ems and their position absolutes. In the olden days of HTML, we arranged everything with table tags and we liked it. Well, some of us did. Mike was recently doing part of a redesign, and when the background color of the page was changed, a bunch of garbage text appeared in various input forms. How could changing the CSS background color cause garbage text to appear?
by Remy Porter on (#4CVHF)
Kara's ongoing quest to tame her codebase continues. First it was serialization, then more strings, then some serial communication.Today, it's threads.The original developer was a physicist and an extremely smart person. They never learned too much about databases, but they knew their way around XML, so they had a simple solution to storing data: any time you wanted to save something, rewrite an entire XML file onto disk.Now, in this case, the "something" being saved is data collected from a piece of scientific equipment. That data is collected by sending commands to the device, changing its state, and asking it for information about readings in that new state.Since this is a complex, long-running process, the developer used threads. Since it's complex and long running, it needs to be stoppable. And this is how they chose to stop it:
by Remy Porter on (#4CS1F)
“My program needs to send some emails,†the developer thought to themselves. The then thought about how this could go wrong, probably thinking that, boy, they’ve got an external server, and boy, spam is a problem, and that server might get upset if you’re sending too many messages at once, or too quickly. That’s a thing which could happen, right?That’s at least a plausible line of thought for the code Juana found, which looks something like this:
by Remy Porter on (#4CPPW)
Matthew D was recently helping a friend plan a trip to Europe from the US. After shopping around a bit, they found a rather affordable airline based out of Poland that fit both their budget and their destination, and started booking a flight.It was going well until it came time for them to enter their passport information. The site complained that the expiry date was invalid. Since that complaint was happening without a page reload, Matthew was pretty sure it was a buggy bit of client-side validation, so he pulled up the dev tools and poked around.
by Mark Bowytz on (#4CHEC)
"Pi...eye...they rhyme, so naturally, I'm qualified to assist Nicole with her make up needs," Dave V. writes.
by Remy Porter on (#4CF2D)
Stored procedures are a bit of a WTF breeding ground. Your average stored procedure language is more limited than your average general purpose language, the syntax is usually clunkier, and everything is so data-focused that implementing logic beyond simplistic processes can be more challenging than one would expect.Of course, this gets harder if you don’t bother to learn how to do string concatenation. Darrin found an example of that while debugging a store procedure:
by Remy Porter on (#4CCQ4)
PHP gets a lot of flack, but perhaps we're taking the wrong perspective on things. Perhaps the gods have condemned PHP to ceaselessly rolling CMSes and wikis up the hill, whence they roll back down under their own weight. The gods had thought, with some reason, that there is no more dreadful punishment than futile and hopeless labor.I mean, look at this code:
by Remy Porter on (#4CA69)
You may remember Karl from a few months back. Karl's organization is notorious for crunch, and it results in some awful sins when you're trying to cram 50 hours of work into the last five hours before launch.Karl didn't write this particular bit, but dreads the day when he has to look at it or change what it does.
 |
by Lorne Kates on (#4C7W4)
Radio WTF Presents!Jump to transcriptWelcome back to Radio WTF. This week, we learn of the power of confidence.Soundcloud Links:Radio WTF: ConfidenceDirect Download:DownloadStarring (in order of appearance)Remy Porter... as Kyle
|
by Mark Bowytz on (#4C2HP)
"Considering the format died out a decade ago, I think I'm going to remove this one from my list and pass on the pre-order," John C. writes.
by Remy Porter on (#4C06A)
Since the dawn of software development, people have endlessly been searching for a way to modularize their applications efficiently. From the “do one thing and do it well (and also everything is text)†protocols of Unix-style command line tools, through to modern microservices, the key idea has always been to have simple, easy to understand components which interface in simple, easy to understand ways. Complex things are built from piles of small, tiny things.Matt W was working on one of those simple modules in a Big Complicated Thing. The Big Complicated Thing was an enterprise “do everything†tool, and like most enterprise tools, it was larger and more complicated than it needed to be. Also, everything talked to everything else in XML, the most enterprise of cross-component interfaces.Over the decades of continuous development, components had proliferated, interfaces had ball-of-mudded together, and seemingly arbitrary silos created boundaries where they didn’t make any sense. To wit, Matt needed to build a report out of the contents of some server-side session variables. Those session variables were populated by another component, which fetched the data from yet another component. Worse, many of those variables were optional, but despite using XML much of the data was stringly typed. Which meant, during testing, Matt saw this in a report:
 |
by Alex Papadimoulis on (#4BY8R)
A couple weeks back, I posted the Free Mug Day campaign: run through the quick BuildMaster tutorial, and I'll send you a free mug. Today, I have a slightly different offer: meet me at InedoCon (Portland, May 22/23) as a TDWTF delegate, and let's chat software over scotch!Why Portland? As part of the mug campaign, I asked everyone to share their feedback/comments/advice, and I got lots of suggestions on how we can improve the software itself. That was great, and then I saw this:
|
by Remy Porter on (#4BXTG)
The realest of real WTFs, the reigning champion for all eternity is and forever will be Oracle. Today, we’re going to take a look at a little code in PL/SQL.PL/SQL is a weird language, a blend of SQL and, well, a Procedural Language, with a side of OO slapped on. The syntax does an excellent job giving you the feeling that it was designed in the 1970s, and each new feature or change to the language continues that tradition.The structure of any PL/SQL code unit is going to be built around blocks. Each block represents a self-contained namespace. The basic anatomy is:
by Remy Porter on (#4BVDN)
Providing authentication for your web-based APIs is both a challenging problem but also a largely solved problem. The hardest part is really just working your way through the various options, and from there it’s usually some variation on a drop-in component.Done properly, it’s also client-agnostic. I can access the service from my browser, I can access it from a thick client, I can access it from cURL. Done incorrectly, well, you get what happened to Amira.She was trying to pull some statistics from the backend, and couldn’t figure out how to authenticate. So she checked the front-end code to see how it authenticated:
 |
by Jane Bailey on (#4BS3E)
If you ask an engineer whether it's safe to cross a bridge, he'll happily walk you through how safe bridges are, how the mathematics work out, how far we've come in structural safety. You'll come away from the conversation feeling confident that no bridge will ever collapse anywhere on the face of the Earth. If you ask a software engineer about banks, however, you'll likely come away terrified, with a 50/50 chance you're now convinced to put all your money in bitcoin. Banks are notorious for bad software decisions—not so much because the decisions are worse, but because most people assume banks are more careful and security-minded.Today's submitter, Kato, worked at Inibank, where they used a commercial product called T24 as the core of their banking system. T24 is used by hundreds of banks worldwide. It's customizable for a wide range of banking solutions, and so like most large customizable suites, there are programmers that specialize in writing custom code for it and consultants that will hold your hand through major upgrades.Inibank brought in a consultant to take on a special project while their resources were busy. At the end of the business day, there is a Close Of Business process that has to be done to ensure all the money gets where it's going, all the appropriate outputs are recalculated, and all the relevant reports are run. In banks, this also changes the system's date to the next working day—which is why if you do online banking on a Sunday, none of it begins to process until Monday morning. The consultant was meant to create a new report that would run during the Close Of Business process, which would do extra processing if it were also the End of Month.Kato sat down with the new guy, showing him how they'd set up their end of day reports. "You see here, there's a global for the last working day, one for today, and one for the next working day. Those are YYMMDD, so they're easier to work with.""Right, right okay, gotcha. Gotcha. And what format is that?""... I don't know the standard off the top of my head, but it's year, month, day.""Right, right, okay. Cool. I'll get right to work, then."Kato walked away from the conversation with a sinking feeling in the pit of his stomach, but he tried to ignore it. The consultant said he was all set up and ready. Surely he knew what he was doing, right? Kato put it out of his mind, and didn't worry about it again until it came time to review the code, and he found this gem:
|
by Mark Bowytz on (#4BKJC)
Adam wrote, "I hear that NewFeature1 is a real, ahem, killer feature of these Wi-Fi drivers."
by Remy Porter on (#4BH5V)
George G was hired to do some UI work for a company which sold a suite of networking hardware. As networking hardware needs to be highly configurable, George was hired on to do “some minor tweaks†to the UI. “It’s just some sizing issues, fonts, the like. I’m sure you’ll do something to the stylesheets or whatever,†said the boss.The boss didn’t know what they were talking about. The UI for some of the products was a web based config tool. That was their consumer-grade products. Their professional grade products used the same Java program which was originally released 15 years earlier. There were no stylesheets. Instead, there was an ancient and wobbling pile of Java Swing UI code, maintained by a “master†who had Strong Opinionsâ„¢ about how that code should look.For example, dispatching a call to a method is indirection. Indirection is confusing. So inline those calls, especially if there's a conditional involved: inline all the “ifsâ€. Factory methods and other tools for constructing complex objects are confusing, so always inline your calls to constructors, and always pass as many parameters as you can, except for the times where you don’t do that, because why would we be consistent about anything?All of the developers on the project had to attend to the master’s wishes during code reviews, where the master gleefully unrefactored code “to make it more clear.â€Also, keep in mind that this UI started back in an era where “800x600†was a viable screen resolution, and in fact, that’s the resolution it was designed against. On a modern monitor, it’s painfully tiny, stuffed with tabs and icons and other UI widgets. Over the years, the UI code has been tweaked to handle edge cases: one customer had the UI zoom turned on, so now there were piles of conditionals to check if the UI needed to be re-laid out. Somebody got a HiDPI display, so again, a bunch of checks and custom code paths, all piled together.Speaking of layout, Swing was a prime case of Java taking object orientation to the extreme, so in addition to passing in widgets you want displayed, you also can supply a layout object which decides how to fill the frame. There was a whole library of them, but if you wanted a flexible layout that also handled screen scaling well, you had to use the most complicated one: Grid Bag. The Grid Bag, as the name implies, is a grid, but where the grid cells can be arbitrary sizes. You control this by adding constraints to the flow. It’s peak Java overcomplification, so even simple UIs tend to get convoluted, and with the “inline all the things†logic, you end up with code like this:
by Remy Porter on (#4BEQK)
Denae inherited some 90s-era GUI code. The original developers have long since gone away, and the source control history has vanished into oblivion. In the 90s, the Standard Template Library for C++ was still very new, so when Denae needs to debug things in this application, it means doing some code archaeology and picking through home-brewed implementations of common data structures.Denae’s most recent bug involved understanding why some UI elements weren’t updating properly. The basic logic the application used is that it maintained a List of GUI items which need to be repainted. So Denae dug into the the List implementation.
by Remy Porter on (#4BC8W)
You may remember Kara, who recently found some "interesting" serialization code. Now, this code happens to be responsible for sending commands to pieces of machine equipment.Low-level machine interfaces remain one of the domains where serial protocols rule. Serial communications use simple hardware and have minimal overhead, and something like RS232 has been in real-world use since the 60s. Sure, it's slow, sure it's not great with coping with noise, sure you have to jump through some hoops if you want a connection longer than 15m, but its failures are well understood.Nothing is so well understood that some developer can't make a mess of it.
 |
by Ellis Morning on (#4B9WP)
Many moons ago, when PCs came housed within heavy cases of metal and plastic, Matt Q. and his colleague were assigned to evaluate a software package for an upcoming sales venture. Unfortunately, he and the colleague worked in different offices within the same metro area. As this was an age bereft of effective online collaboration tools, Matt had to travel regularly to the other office, carrying his PC with him. Each time, that meant unscrewing and unhooking the customary 473 peripheral cables from the back of the box, schlepping it through the halls and down the stairs, and catching the bus to reach the other office, where he got to do all those things again in reverse order. When poor scheduling forced the pair to work on the weekend, they hauled their work boxes between apartments as well.As their work proceeded, Matt reached the limits of what his 20 MB hard drive could offer. From his home office, Matt filed a support ticket with IT. The technician assigned to his ticket—Gary—arrived at Matt's cubicle some time later, brandishing a new hard drive and a screwdriver. Gary shooed Matt away for more coffee to better focus on his patient. One minor surgery later, Matt's PC was back up and running with a bigger hard drive.One day ahead of the project deadline, Matt was nearly done with his share of the work. He just had a few tweaks to make to his reports before copying them to the floppy disks needed by the sales team. Having hooked his PC back up within his cubicle, he switched it on—only to be greeted with a literal bang. The PC was dead and would not start.After a panicked call to IT, Gary eventually reappeared at his desk with a screwdriver. Upon cracking open the PC case, he immediately cried, "Wait a minute! Have you been carting this PC around?"Matt frowned. "Er, yes. Is that a problem?""I'll say! You weren't supposed to do that!" Gary scolded. "The hard drive's come loose and shorted out the workings!"Matt darted over to Gary's side so he could see the computer's innards for himself. It didn't take long at all to notice that the new hard drive had been "secured" into place using Scotch tape."Hang on! I daresay you weren't supposed to do that!" Matt pointed to the offending tape. "Shall I check with your manager to be on the safe side?"Gary's face crumpled. "I don't have access to the proper mountings!""Then find someone who does!"Armed with his looming deadline and boss' approval, Matt escalated his support ticket even higher. It didn't take long at all for genuine mounting brackets to replace the tape. He never learned why IT techs were being deprived of necessary hardware; he assumed it was some fool's idea of a brilliant cost-cutting measure. He had to wonder how many desperate improvisations held their IT infrastructure together, and how much longer they would've gone unnoticed if it hadn't been for his PC-toting ways. [Advertisement] Forget logs. Next time you're struggling to replicate error, crash and performance issues in your apps - Think Raygun! Installs in minutes. Learn more.
|
by Mark Bowytz on (#4B4CE)
Neil S. wrote, "MSN UK's reverse psychology marketing angle is pretty edgy."
by Remy Porter on (#4B1W4)
Ignoring current events, England and the rest of Europe have had a number of historical conflicts which have left a number of grudges littered across the landscape.Andro V lives in Norway, but is remotely collaborating with an English developer. That English developer wants their peers to know that Sweyn I and Thorkell the Tall’s invasions of southern England will never be forgotten.
 |
by Bobby T. Johnson on (#4AZ7A)
People like hot dogs until they see how it's made. Most people don't ask, because they don't want to know and keep eating hot dogs. In software, sometimes we have to ask. It's not just about solving problems, but because what scares some programmers is the knowledge that their car's software might be little more than the equivalent of driving duct-taped toothpicks down the highway at 70MPH. Our entire field is bad at what we do.Brett worked as a system analyst for a medical research institution, MedStitute. MedStitute used proprietary software for data storage and analysis, called MedTech. Doctors and researchers like MedTech's results, but Brett his co-worker Tyree- know how it's made.The software has no backend access, and all software development happens in a "click-to-program" GUI. The GUI looks like it was built from someone who learned to code by copy/pasting from 1990s era websites, watching ten minutes of Jurassic Park, and searching StackOverflow until something compiled. The "language" shows the same careful design philosophy. Every if must have an else. Some modules use booleans, some return an empty string to represent false values. Documentation is unclear about which situation is which. Essentially, every if statement becomes three statements.Brett needed to launch a new study. A study depends on some basic set of statistics and groups patients based on a randomized variable. Brett looked through the list of variables he could randomize on, and the one he wanted was missing. Brett assumed he made a mistake, and went back a few screens to check the name, copying it down for reference. He went back to the list of randomizable variables. It wasn't there. He looked closer at the list. He noticed that the list of randomized variables only included data from multiple-choice fields. The field he wanted to randomize on was based on a calculated field.Brett knew that Tyree had worked on another project that randomized on a calculated field, so he messaged Tyree on Slack. "How did you code this random variable? In Medtech it won't let you?""I'm on a conference call, let me call you afterward," Tyree wrote.A few minutes later, Tyree called Brett."What you have to do is start with two fields. Let's call it $variable_choice, that's a multiple choice question, and $variable_calced that's your calculated field. When you want to create a variable that randomly selects based on your calculated field, you start by telling Medtech that this random variable is based on $variable_choice. Then you delete $variable_choice, and then rename $variable_calced to be $variable_choice.""Wait, they allow you to do that, but don't allow you to randomize calculated fields any other way? And they don't check?""Hopefully, they don't decide to start checking before this project is over," Tyree said."This study is supposed to go on for ten years. This project succeeding comes down to them never treating this workaround as a bug?""It was the only solution I could find. Let me know if you need anything else?"Brett wasn't completely satisfied with the hack and went back to the documentation. He found a "better" solution: he could make a read-only multiple-choice field with only one choice, the value of the calculated field, as the default answer. Unfortunately, it was possible that the user would alter the list unintentionally by answering the multiple-choice question before the calculated field was evaluated.Ultimately, the only choice left to Brett was to take his lunch break, go to the cafeteria, and order two hot dogs. [Advertisement] Utilize BuildMaster to release your software with confidence, at the pace your business demands. Download today!
|
by Remy Porter on (#4AWMB)
“We know that governmental data-systems aren’t generally considered ‘cutting edge’ or ‘well architected’, but we’ve brought together some top flight talent, and we’re building a RESTful architecture that guarantees your code gets nice, easy-to-consume JSON objects.â€That’s what Oralee B. was told when she was hired to work on it. The system owned pretty much the entirety of the municipal data management market, tracking birth certificates, marriage certificates, death certificates and pet licenses for nearly every city in the country. JSON is so simple, how can you screw it up?The same way most people seem to screw it up: reinventing key/value pairs in your key/value data format.
by Remy Porter on (#4AT54)
Mike inherited a data-driven application. Once upon a time, it started out pretty well architected. Yes, it was in PHP, but with good architecture, solid coding practices, and experienced developers, it was simple and easy to maintain.Time passed. The architects behind it left, new developers were hired, management changed over, and it gradually drifted into what you imagine when you hear "PHP app" in 2019.Mike's task was to start trying to clean up that mess, and that started all the way back in the database layer with some normalization. From there, it was the arduous task of going through the existing data access code and updating it to use the refined model objects.While there was a mix of "already uses a model" and "just a string" SQL statements in the code, there was a clear data-access layer, and almost all of the string-based queries actually used parameters. At least, that was true until Mike took a look at the "god" page of the application.You know how it is. Thinking through features and integrating them into your application is hard and requires coordinating with other team members. Slapping together a page which can generate any arbitrary SQL if you understand how to populate the drop-downs and check boxes correctly is "easy"- at least to start. And by the time it gets really hard, you've already created this:
by Mark Bowytz on (#4AMP7)
Michael P. wrote, "Only two minutes and a couple of blocks from my destination, Waze decided I should take a 2-hour, 80-mile detour."
by Remy Porter on (#4AJ75)
Sometimes, the best defense is a good offense. Other times, the best offense is a good defense. And if you’re not sure which is which, you’ll never be a true strategic mastermind.Tina’s co-worker understands that this is true for defensive programming. Always, always, always catch exceptions. That’s a good defense.
 |
by Alex Papadimoulis on (#4AG6R)
Long time, no mug! It's been an insanely long time since we've held a Free TDWTF Mug Day. So long that I'm sure most of you have forgotten the joy that is free mug day. Here's how it works:I've been pretty excited about BuildMaster 6.1, in part because it returns the product to my original vision of helping developers focus on writing great software instead of worrying about how to build, test, and deploy it from source code to production. Or, CI/CD as we'd call it today.I'd love to get your feedback on the release, and perhaps ideas on how I can work to improve the product. If you'd be willing to help me, I'll send you one of these beautiful, oversized TDWTF mugs, as modeled by Jawaad M:To get one, all you have to do is either download/install BuildMaster or spin up our pre-made virtual machine(AMI) image, then run through this quick configuration and fill out this form with your name, address, etc. It should take all of 15 minutes or so to complete.Everything's free, and there's no credit card needed, or anything like that. In fact, you can keep using BuildMaster for free if you'd like -- there's no server, application, or even user limit.This offer expires on March 31, 2019, and supply is limited to 250, so sign up soon! To get started, just follow this link and, in a few weeks time, you'll not only be more knowledgeable about BuildMaster, but you'll be enjoying beverages much more fashionably with these nice, hefty The Daily WTF mugs. [Advertisement] BuildMaster allows you to create a self-service release management platform that allows different teams to manage their applications. Explore how!
|
by Remy Porter on (#4AFNF)
A lot of ink has been spilled talking about the perils and pitfalls of offshore development. Businesses love paying the wage arbitrage game, and shipping software development tasks to an outside vendor and paying half the wage they would for a dedicated employee.Of course, the key difference is the word “dedicatedâ€. You could have the most highly skilled offshore developer imaginable, but at the end of the day: they don’t care. They don’t care about you, or your business. They don’t care if their code is good or easy to maintain. They’re planning to copy-and-paste their way up the ranks of their business organization, and that means they want to get rotated off your contract onto whatever the next “plum†assignment is.Jules H worked for a company which went so far as to mandate that every project needed to leverage at least one offshore resource. In practice, this meant any project of scale would shuffle through half a dozen offshore developers during its lifetime. The regular employees ended up doing more work on the project than they would have if it had been developed in-house, because each specification had to be written out in utterly exhaustive detail, down to explaining what a checkbox was, because if you simply told them to add “a checkboxâ€, you’d get a dropdown or a text area instead.Jules got called in when someone noticed that the “save†functionality on one page had completely broken. Since the last change to that application had been a year ago, the feature hadn’t been working for a year.The page used a client-side MVC framework that also tied into a .NET MVC view, and due to the way the page had been implemented, all the client widgets treated everything as stringly typed (e.g., "true", not true), but all the server-side code expected JSON data with real types.The code which handled this conversion was attempting to access a field which didn’t exist, and that was the cause of the broken save functionality. That was easy for Jules to fix, but it also meant he had to take a look at the various techniques they used to handle this stringly-typed conversion.
by Remy Porter on (#4AD4V)
Inheritance is one of those object-oriented features whose importance is perhaps overstated. When I was first being introduced to OO, it was a lot of “code reuse!†and “polymorphism!†and “code reuse!†In practice, inheritance is usually a way to tightly couple two different classes and create more headaches and rework in the future.That’s why many OO languages favor interfaces, and why the classic Gang-of-Four patterns emphasize the importance of composition in many situations. And, because inheritance can make things complicated, most languages also require single parent inheritance.Most languages. C++, on the other hand, doesn’t. In C++, I could define a class Car, a class Truck, and then do this:
by Remy Porter on (#4AARD)
Parallel programming is hard. For all the advancements and tweaks we've made to our abstractions, for all the extra cores we've shoved into every CPU, deep down, software still carries the bias of the old uni-tasking model.Aleksei P works on a software package that is heavily parallel. As such, when interviewing, he talks to candidates about their experience with .NET's Task objects and the async/await keywords.One candidate practically exploded with enthusiasm when asked. "I've just finshed a pretty large text processing project that reads a text file in parallel!" They whipped out a laptop, pulled up the code, and proudly showed it to Aleksei (and gave Aleksei a link to their repo for bonus points).